| Home | https://dragonic.eu |
| Bluesky (fun art account) | https://bsky.app/profile/dragoonaethis.bsky.social |
Dragoon Aethis
- 51 Followers
- 93 Following
- 369 Posts
This is quite awesome - successful Xbox One ROM glitching, by Markus "doom" Gaasedelen: https://www.youtube.com/watch?v=FTFn4UZsA5U
Congratulations!

RE//verse 2026: Hacking the Xbox One
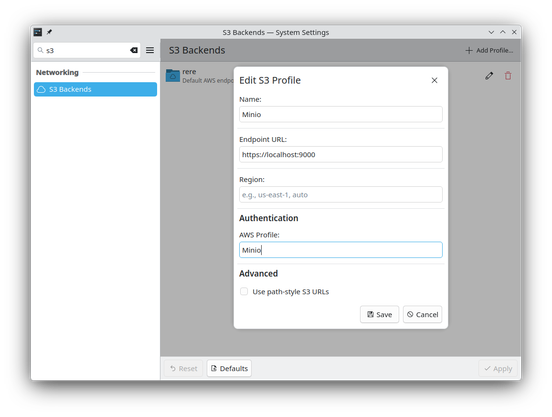
It’s now possible to access files in S3 (or any compatible services) with Dolphin and other @kde apps! We just released the first version of KIO S3, which bridges S3 with all KIO-powered apps.

Pickmon - Offical Trailer

Hacking the Xbox One
Launched in 2013, the Xbox One's security story is often reduced to a single word: unhackable. Beneath that banner is a security architecture where every obvious target is both hardened by platform-specific mitigations and disposable: usermode, kernel, hypervisor, and system firmware are independently protected, signed, and bound to a morphing key tree, so exploiting one version doesn’t buy you the ability to decrypt or run future updates and content. Only one piece of critical code lies outside that safety net: the tiny, carefully constructed bootrom of the Platform Security Processor, burned directly into the system's custom AMD SoC. Microsoft engineered the bootrom as a fortress: a minimal-complexity, hardened core with purpose-built hardware countermeasures, fault-tolerant software patterns, randomized stalls, and layered runtime redundancy to maintain tight control over the earliest boot stage. As the anchor for the entire chain of trust, this code is expected to perform a measured cryptographic boot while withstanding multiple targeted glitches from a persistent physical attacker, detecting power, memory, and control-flow irregularities to avoid compromise. This bootrom represents an unprecedented escalation in platform security, offering only the faintest side channels to study its execution. Every experiment becomes a patient probe: a guided reverse-engineering effort stacking scraps of signal, reading the tea leaves of carefully shaped faults, and weaponizing subtle side effects – all to wrest control of a legendary security core and shatter the Xbox One chain of trust once and for all. When you whisper your secrets into the dark heart of the system and, for the first time in history, it whispers back, "unhackable" starts to sound less like a property… and more like a challenge.