| Keybase | https://keybase.io/DFIR |
| YouTube | https://www.youtube.com/c/AliHadiC5W |
| dfir @ protonmail.com |
Ali Hadi | B!n@ry
- 572 Followers
- 54 Following
- 65 Posts
The course is being used by LE agencies, university professors, and many other professionals. If you have any feedback? You are very welcome to share with us. Read more about the decision and URL to the course below. #DFIR #Cybersecurity #infosec
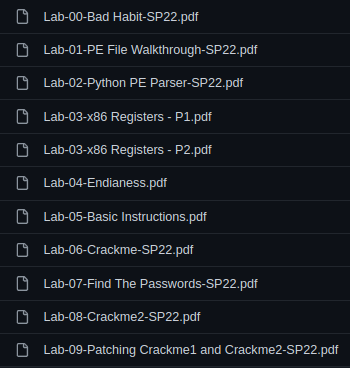
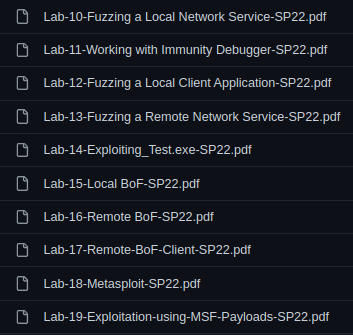
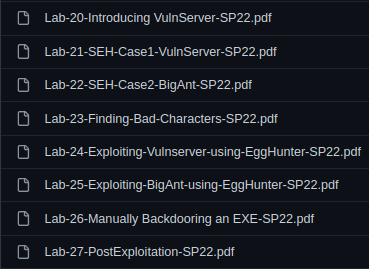
Just finished uploading the final set of labs that are published publicly. That's all folks for now. Hope they will be useful to someone out there!... #RE #Offsec #ExploitDev #SoftwareExploitation
Since some are only on Mastodon. I wanted to share my Offensive Security & Reverse Engineering (OSRE) course labs (docx) which I uploaded to my repo found below. Most of them have very detailed instructions and should be great to get you started in Software Exploitation. They are not just good for software exploitation, but even learning about debugging & diff x86 instructions. There are some assembly quizzes which might be useful, I'll share those too. You can find them under the line saying "Labs 2022 can be found here"
Repo: https://exploitation.ashemery.com
Videos (EN): https://www.youtube.com/playlist?list=PLCS2zI95IiNybAAQ0HL88YzwRpLXje5y6
Videos (AR): https://www.youtube.com/playlist?list=PLCS2zI95IiNyo5AhbVIL2hVX7zhuSkOkz
#Offsec #SoftwareExploitation #RE
That's it for 2022 ... Good luck you all with 2023 :)
A few people have asked me about the #LastPass incident. I don't really have anything new to add but stand by this article I wrote a few years ago!
https://netresec.com/?b=18C38eb
TorPCAP - Tor Network Forensics
Unencrypted network traffic, destined for the Tor network, is sent between localhost TCP sockets on computers running Tor clients, such as the Tor Browser. In this blog post I show how anonymous Tor browsing can be visualized, by loading a PCAP file with localhost traffic into NetworkMiner. We call[...]
Extremely kind interview by Alex Muldwych. We talk about #DFIR, #Python, and the importance of time, among other things.
Check it out here:
https://thesecuritynoob.com/interviews/interview-with-dfir-legend-alexis-brignoni/