GrapheneOS will remain usable by anyone around the world without requiring personal information, identification or an account. GrapheneOS and our services will remain available internationally. If GrapheneOS devices can't be sold in a region due to their regulations, so be it.
It’s very funny that gaming community was turned into a mdern frontier of rootkit/bootkit development — the most interesting projects that I seen recently are related to either cheats or anti-cheats
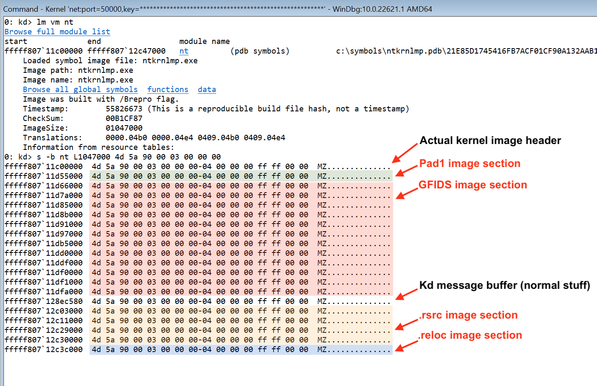
Fortunately, it's quite trivial to bypass this "mitigation" by verifying sections list of the "fake" images against actual PE sections that normally presents in the kernel image. Keep this stuff in your mind while working on kernel exploits, DIFR tools, DMA attacks and other things where it may be relevant :)
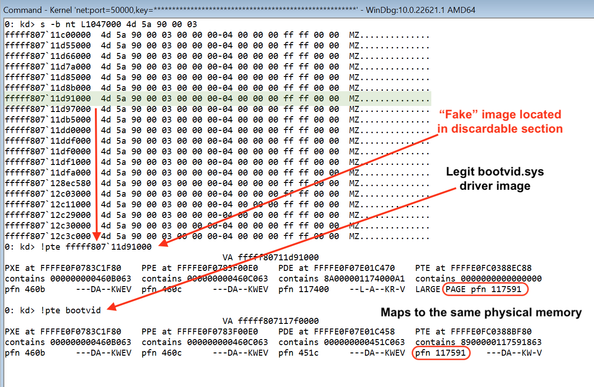
The fake PE images shown above aren't "real" memory allocations, but rather dual mappings of already loaded legitimate images, and they seem to be randomized on every boot. I'm not sure why exactly it's done, but likely to screw up kernel exploit primitives like "using memory scanning to determine the kernel base address from a leaked pointer", since it's impossible to get the kernel base address from a low-privileged process on modern versions of Windows 2/2
While playing with my Hyper-V backdoor on Windows Server 10.0.20348 test machine I noticed some pretty unexpected memory content in the discardable sections of PE images belonging to the NT kernel. It turns out that on modern systems the kernel plants "fake" PE images into these sections, which normally shouldn't be mapped at all due to the IMAGE_SCN_MEM_DISCARDABLE attribute 1/2
It seems that IDA Pro with version 9.3 finally reached maturity level of the Visual Studio -- you're using old version not because you like it more, but because it doesn't have UI lags 😬
LMAO, you apparently can encode “trigger refusal” magic string and it will still work
RE: https://mastodon.social/@d_olex/116063927799976625
An example of C code, ASM code generated by gcc -O3 and produced REIL code after optimization passes for one of the tests: https://gist.github.com/Cr4sh/a49254ae5ca2a91b488574b6aaae5c29
Another interesting outcome of this experiment -- models are good, tooling is shit. I'm more than happy with the quality of LLMs, but all of the infrastructure around them like SDKs, libraries, clients, MCPs and stuff is very buggy and immature: you have to roll your own things to make it work well