The recording of my second Binary Cartography webinar is public:
Agentic Malware Analysis: From Task Automation to Deep Analysis
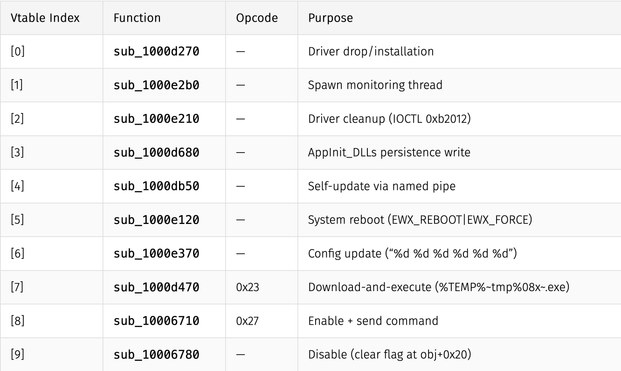
Topics: string decryption, API hashing, unpacking & pipeline building
Recording: https://youtu.be/azej1P17w9E
Slides & samples: https://github.com/mrphrazer/binary-cartography/tree/main/2026-04-agentic_malware_analysis