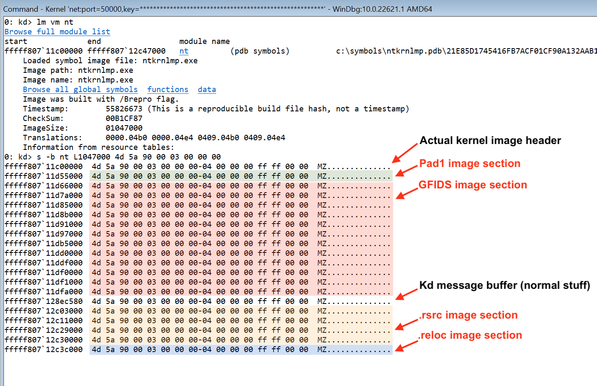
While playing with my Hyper-V backdoor on Windows Server 10.0.20348 test machine I noticed some pretty unexpected memory content in the discardable sections of PE images belonging to the NT kernel. It turns out that on modern systems the kernel plants "fake" PE images into these sections, which normally shouldn't be mapped at all due to the IMAGE_SCN_MEM_DISCARDABLE attribute 1/2
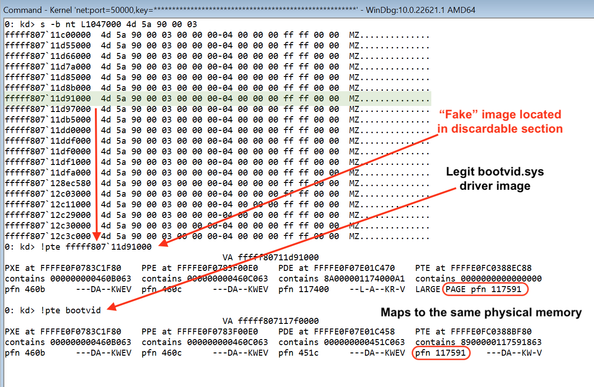
The fake PE images shown above aren't "real" memory allocations, but rather dual mappings of already loaded legitimate images, and they seem to be randomized on every boot. I'm not sure why exactly it's done, but likely to screw up kernel exploit primitives like "using memory scanning to determine the kernel base address from a leaked pointer", since it's impossible to get the kernel base address from a low-privileged process on modern versions of Windows 2/2
Fortunately, it's quite trivial to bypass this "mitigation" by verifying sections list of the "fake" images against actual PE sections that normally presents in the kernel image. Keep this stuff in your mind while working on kernel exploits, DIFR tools, DMA attacks and other things where it may be relevant :)