Cyber Slayer
- 11 Followers
- 129 Following
- 312 Posts
State control of big media is one of the first steps to total consolidation of power.
Good morning dear astonishing Tooteroonies of this n that☕🌞
Moonday n after time switch dark again🥴 a new one ahead tho😉
I wish yous a fabulous day full of happiness, kindness, optimism, insight, wisdom, knowledge, magic, camaradery, hope, funs, joys, smiles n laughter😊🤙
#Moonday #MorningGreetings #Smiles
Moonday n after time switch dark again🥴 a new one ahead tho😉
I wish yous a fabulous day full of happiness, kindness, optimism, insight, wisdom, knowledge, magic, camaradery, hope, funs, joys, smiles n laughter😊🤙
#Moonday #MorningGreetings #Smiles
The FCC’s WiFi router ban is “an extremely blunt instrument, and it’s going to impact many harmless products in order to stem a real problem,” EFF’s @legind told CNET. https://www.cnet.com/home/internet/fcc-bans-foreign-made-routers-as-national-security-risk/
RE: https://wetdry.world/@ihatecompvir/116289367138743369
All I know is :q! to exit without saving changes
Since you all asked nicely: the large vertical prints are available - either as a physical print shipped by me with my stamp on, *or* as a digital file so you can print it yourself because shipping costs are poopoo and nobody wants to pay them (understandably)
Physical print:
https://doombloomart.com/products/no-ai-support-human-artists-nouveau-art-print
RE: https://xoxo.zone/@ilovecomputers/116275772384259836
No, seriously - I can't possibly overstate the value in my life that has come from the internet or how it has enriched me.
Like Ed Zitron & @pluralistic have both written about at various times, I'm not mad at technology - I'm fucking furious at the fuckfaces who deliberately ruined it, just so they could squat their ignoble asses upon a mountain of riches like the shittiest, saddest little saggy dragons imaginable.
That's not just more 🇨🇦 state surveillance.
In 2024, Chinese state hackers broke AT&T+Verizon through a similar backdoor. 1 mil+ people's data was compromised.
Coming soon to 🇨🇦 through #BillC22.
The data broker industry must be destroyed: https://www.theverge.com/news/897145/kash-patel-ron-wyden-fbi-location-data-no-warrant
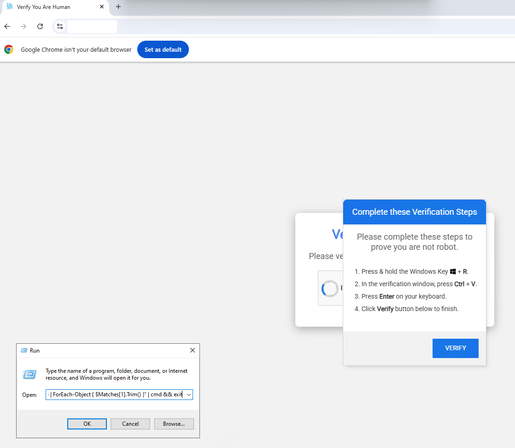
Threat Actors are "Bringing Their Own Forensics"
In a recent ClickFix campaign, we saw threat actors likely related to Interlock Ransomware, running Volatility (https://vol.py) directly on victim machines.
Commonly a tool for defenders, the threat actors are using it to:
➡️Dump RAM: Capturing mem.raw from the infected host.
➡️Extract Hashes: Using windows.hashdump to pull NTLM hashes.
➡️Steal Credentials: Using windows.cachedump to extract cached creds.
After years of planning a potential collab, I finally got to sit down with fellow cybersecurity YouTuber David Bombal for an in person interview! Below you can check out the video from what will hopefully be the first of many more collaborations 😃 :
https://www.youtube.com/watch?v=KsXzTz5H2QQ
https://www.youtube.com/watch?v=KsXzTz5H2QQ
 🏳️🌈🖖🏽
🏳️🌈🖖🏽