Threat Actors are "Bringing Their Own Forensics"
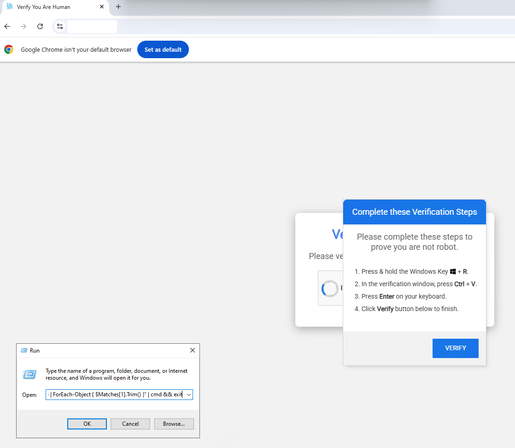
In a recent ClickFix campaign, we saw threat actors likely related to Interlock Ransomware, running Volatility (https://vol.py) directly on victim machines.
Commonly a tool for defenders, the threat actors are using it to:
➡️Dump RAM: Capturing mem.raw from the infected host.
➡️Extract Hashes: Using windows.hashdump to pull NTLM hashes.
➡️Steal Credentials: Using windows.cachedump to extract cached creds.