| Website | https://nopcorn.github.io |
| Github | https://github.com/nopcorn |
| CuteRAT 🐭 | https://github.com/nopcorn/CuteRAT |
nopcorn
- 41 Followers
- 104 Following
- 152 Posts
Malvertiser Copies Pc News Site To Deliver Infostealer - https://www.redpacketsecurity.com/malvertiser-copies-pc-news-site-to-deliver-infostealer-2/
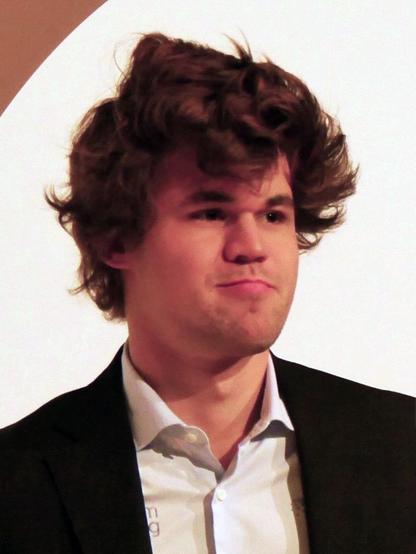
Happy birthday Magnus #Carlsen! 🥳
Countless achievements across his career (such as 5 World Championship Titles), but we cannot fail to mention the first Lichess #TitledArena ever! 😁
#cybersecurity #infosec #advisory #vulnerability
https://beyondmachines.net/event_details/exploit-proof-of-concept-released-for-crushftp-patch-asap-u-i-s-c-b/gD2P6Ple2L
A couple of blog posts for learning about Linux process injection (specifically sshd injection for credential harvesting)
https://blog.xpnsec.com/linux-process-injection-aka-injecting-into-sshd-for-fun/
Linux ptrace introduction AKA injecting into sshd for fun
If there is one thing I've come to appreciate over this past few weeks, it's just how much support you are provided from the Win32 API. That being said, I wanted to tackle some Linux process injection, with the aim of loading a shared object into another process address space without having to resort to LD_PRELOAD, or stopping the process. The goal I set myself was quite simple, could I recover plain text credentials from the sshd process using ptrace. Granted, this is a bit of an arbitrary goa