RE: https://infosec.exchange/@ifin/116540679223847150
If anyone has more information on this, DMs are open.
Cybersecurity reporter for Risky Business
#infosec #cybersecurity #security
| Newsletter: | https://risky.biz/newsletters/ |
| Podcast: | https://risky.biz/podcasts/ |
RE: https://infosec.exchange/@ifin/116540679223847150
If anyone has more information on this, DMs are open.
and we have another one. This one with CVE.
#dirtyfrag #CVE-2026-43500
-Google patches Android remote takeover bug
-Palo Alto Networks patches firewall zero-day
-Ivanti also patches one
-Leak exposes Russia's spy and hacker school
-US includes offensive cyber in counterterrorism strategy
-US hasn't forgotten about CISA 2015
-EU working to exclude US firms from EU clouds
-Five water treatment stations hacked in Poland
-Pegasus investigation reopened in Barcelona
Podcast: https://risky.biz/RBNEWS561/
Newsletter: https://news.risky.biz/risky-bulletin-google-patches-android-remote-takeover-bug/
New, from me: Canvas Breach Disrupts Schools and Colleges Nationwide
"An ongoing data extortion attack targeting the widely-used education technology platform Canvas disrupted classes and coursework at school districts and universities across the United States today, after a cybercrime group defaced the service’s login page with a ransom demand that threatened to leak data from 275 million students and faculty across nearly 9,000 educational institutions."
"Canvas parent firm Instructure responded to today's defacement attacks by disabling the platform, which is used by thousands of schools, universities and businesses to manage coursework and assignments, and to communicate with students."
Lots more here:
https://krebsonsecurity.com/2026/05/canvas-breach-disrupts-schools-colleges-nationwide/
It would appear that the DDoS attack affecting #Ubuntu is finally over, with statements from both Canonical and the claimed attackers. While the attackers threaten Cloudflare next, they continue to use their services to protect their booter service. Meanwhile, Canonical has not put anything but security and archive repos behind Cloudflare protection. It's unknown what other measures are in place for other resources.
https://discourse.ifin.network/t/ubuntu-services-under-attack/356
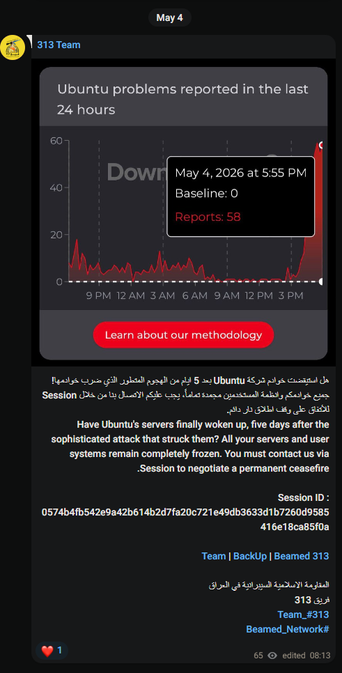
Last Updated: 2026-05-04T17:46:49Z (UTC) Status page notes security and archive are down again. https://status.canonical.com Canonical now has an official forum thread for this incident: Impacted: security.ubuntu.com jaas.ai archive.ubuntu.com canonical.com maas.io blog.ubuntu.com developer.ubuntu.com Ubuntu Security API-CVEs Ubuntu Security API-Notices academy.canonical.com ubuntu.com portal.canonical.com assets.ubuntu.com launchpad.net livepatch.canonical.com Cause Unconfirmed, but...
The 3 recent Linux LPEs are sort of interesting in that each one took a different path from discovery to disclosure.
linux-distros mailing list. But the embargo was broken, so it was disclosed unexpectedly ahead of time.Each path had basically exactly the same outcome (No fixes at publication time). 😂