The value-proposition of building and maintaining an internal Threat Hunting team...
Austin
- 32 Followers
- 147 Following
- 333 Posts
CrowdStrike complained to Cloudflare about a CrowdStrike parody site… and Cloudflare took it down. Without a court order. https://clownstrike.lol/crowdmad/
Cloudflare recently announced they have become a strategic partner with CrowdStrike: https://www.cloudflare.com/en-gb/press-releases/2024/crowdstrike-and-cloudflare-announce-expanded-strategic-partnership-to-secure/
🌟 Since the release of GPTs many people started to experiment with their own agent, which allows to craft a bot for a specific use case.
🛡️ Yesterday I created an 'Awesome' repository that catalogs all the GPTs used for cybersecurity. And the list keeps growing!
Have a look to it and feel free to add yours! 👇 #infosec #gpts #ia #llms
Breaking Into DFIR: Is It Entry-Level? With Special Guest Jessica Hyde
Robby East - Center Of Gravity
Tickets are on sale now for This Never Happened Presents Australia. https://thisneverhappened.ffm.to/live Robby East returns to the label with the single 'Center Of Gravity' Stream: https://thisnever
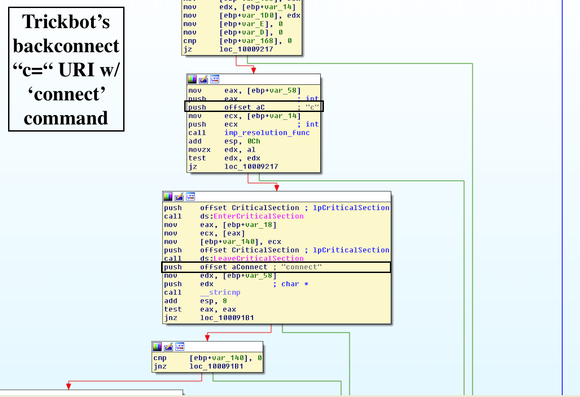
#TrickBot #TeamSpy #Socks5Systemz
https://vk-intel.org/2017/11/21/lets-learn-trickbot-socks5-backconnect-module-in-detail/
Recorded Future has a report on how Chinese APTs have evolved over time.
The report also includes this map of the suspected locations of Chinese APT groups.
https://www.recordedfuture.com/charting-chinas-climb-leading-global-cyber-power
The operators of the Kinsing malware are targeting cloud environments with systems vulnerable to "Looney Tunables," a Linux security issue identified as CVE-2023-4911 that allows a local attacker to gain root privileges on the system.
Hackers exploit Looney Tunables Linux bug, steal cloud creds
The operators of the Kinsing malware are targeting cloud environments with systems vulnerable to "Looney Tunables," a Linux security issue identified as CVE-2023-4911 that allows a local attacker to gain root privileges on the system.