Andy Boyko
- 57 Followers
- 385 Following
- 110 Posts
Back in 1996, I archived Prince's own first-person narrative of why he changed his name, which he briefly published on his website and then quickly pulled down. After his passing, I brought it back online for the first time in two decades.The long-lost "Message from The Artist": https://medium.com/@anildash/message-from-the-artist-c611535da21c
"I was beyond frustrated with my lack of control over my career and music."
Oh my god. This is a graphic depiction of how I found out that unicorns aren't real.
I asked my elementary school librarian for a “real” book about unicorns, because I couldn’t find any in the nonfiction section, near the other animal books.
She gently informed me that all of the books about unicorns were in the fiction section, and allowed me to draw my own (devastating) conclusion. 😔
Many of you have been asking for my thoughts on the #LastPass breach, and I apologize that I'm a couple days late delivering.
Apart from all of the other commentary out there, here's what you need to know from a #password cracker's perspective!
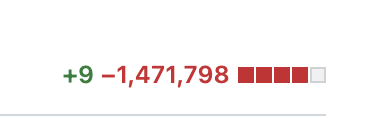
Your vault is encrypted with #AES256 using a key that is derived from your master password, which is hashed using a minimum of 100,100 rounds of PBKDF2-HMAC-SHA256 (can be configured to use more rounds, but most people don't). #PBKDF2 is the minimum acceptable standard in key derivation functions (KDFs); it is compute-hard only and fits entirely within registers, so it is highly amenable to acceleration. However, it is the only #KDF that is FIPS/NIST approved, so it's the best (or only) KDF available to many applications. So while there are LOTS of things wrong with LastPass, key derivation isn't necessarily one of them.
Using #Hashcat with the top-of-the-line RTX 4090, you can crack PBKDF2-HMAC-SHA256 with 100,100 rounds at about 88 KH/s. At this speed an attacker could test ~7.6 billion passwords per day, which may sound like a lot, but it really isn't. By comparison, the same GPU can test Windows NT hashes at a rate of 288.5 GH/s, or ~25 quadrillion passwords per day. So while LastPass's hashing is nearly two orders of magnitude faster than the < 10 KH/s that I recommend, it's still more than 3 million times slower than cracking Windows/Active Directory passwords. In practice, it would take you about 3.25 hours to run through rockyou.txt + best64.rule, and a little under two months to exhaust rockyou.txt + rockyou-30000.rule.
Keep in mind these are the speeds for cracking a single vault; for an attacker to achieve this speed, they would have to single out your vault and dedicate their resources to cracking only your vault. If they're trying 1,000 vaults simultaneously, the speed would drop to just 88 H/s. With 1 million vaults, the speed drops to an abysmal 0.088 H/s, or 11.4 seconds to test just one password. Practically speaking, what this means is the attackers will target four groups of users:
1. users for which they have previously-compromised passwords (password reuse, credential stuffing)
2. users with laughably weak master passwords (think top20k)
3. users they can phish
4. high value targets (celebs, .gov, .mil, fortune 100)
If you are not in this list / you don't get phished, then it is highly unlikely your vault will be targeted. And due to the fairly expensive KDF, even passwords of moderate complexity should be safe.
I've seen several people recommend changing your master password as a mitigation for this breach. While changing your master password will help mitigate future breaches should you continue to use LastPass (you shouldn't), it does literally nothing to mitigate this current breach. The attacker has your vault, which was encrypted using a key derived from your master password. That's done, that's in the past. Changing your password will re-encrypt your vault with the new password, but of course it won't re-encrypt the copy of the vault the attacker has with your new password. That would be impossible unless you somehow had access to the attacker's copy of the vault, which if you do, please let me know?
A proper mitigation would be to migrate to #Bitwarden or #1Password, change the passwords for each of your accounts as you migrate over, and also review the MFA status of each of your accounts as well. The perfect way to spend your holiday vacation! Start the new year fresh with proper password hygiene.
For more password insights like this, give me a follow!