| Subreddit | https://reddit.com/r/netsec |
| Automated by | @[email protected] |
/r/netsec
- 1.4K Followers
- 0 Following
- 6.3K Posts
Follow for new posts submitted to the netsec subreddit. Unofficial.
Responsible disclosure is structurally dead — not dying. Here's the analysis and what replaces it. https://www.thecrucible.systems/whitepapers/f27bb2aa-8a5b-47d3-b3bf-b33effa7e20e
Using Cloudflare’s Post-Quantum Tunnel to Protect Plex Remote Access on a Synology NAS https://infosecwriteups.com/using-cloudflares-post-quantum-tunnel-to-protect-plex-remote-access-on-a-synology-nas-5745ae8b085e
Trivy supply chain attack enabled European Commission cloud breach https://www.helpnetsecurity.com/2026/04/03/european-commission-cloud-breach/
Closing the Kernel Backport Gap: Automated CVE Detection https://hardenedlinux.org/blog/2026-04-06-closing-the-kernel-backport-gap-automated-cve-detection-for-the-eu-cra-cyber-resilience-act/
Cracking a Malvertising DGA From the Device Side https://www.buchodi.com/cracking-a-malvertising-dga-from-the-device-side/
Cracking a Malvertising DGA From the Device Side
When piracy streaming sites inject third-party JavaScript into your browser, the domains hosting that JavaScript are designed to be invisible. They rotate every three hours, use algorithmically generated names on cheap TLDs, and vanish before anyone notices them. I cracked the algorithm that generates them. Using application-layer traffic from mobile
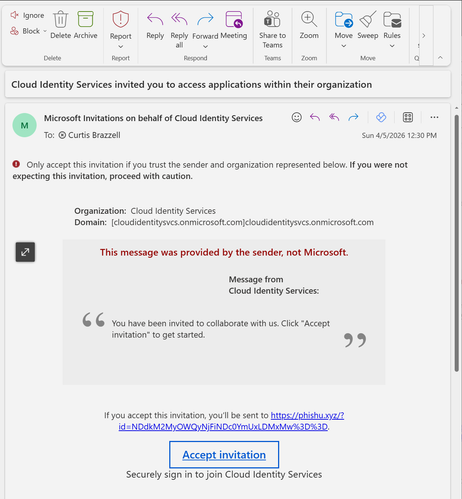
The Attack With No Attacker Domain: Microsoft Entra B2B Guest Invitation Phishing https://phishu.net/blogs/blog-microsoft-entra-b2b-guest-invitation-phishing-phishu-framework.html
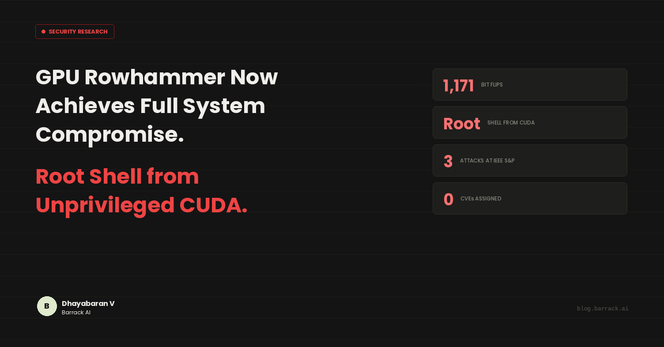
GDDRHammer and GeForge: GDDR6 GPU Rowhammer to root shell (IEEE S&P 2026, exploit code available) https://blog.barrack.ai/gddrhammer-geforge-gpu-rowhammer-gddr6/
36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants https://realnarrativenews.com/read/36-malicious-npm-packages-exploited-redis%2C-postgresql-to-deploy-persistent-implants/
I have refactored slurp s3 bucket enumerator to work with any s3 compatible cloud https://codeberg.org/nwcs/slurp
BrowserGate: LinkedIn/Microsoft allegedly scans 6,000+ browser extensions & links them to real identities, all without user consent https://thecybersecguru.com/news/browsergate-linkedin-microsoft-espionage-report/