How to Evaluate an npm Package - 2026 Edition
Stars and downloads tell you about popularity, not safety. Here's a practical checklist for evaluating an npm package's security, reliability, and long-term maintenance in 2026.
 YouTube
YouTube1,001 IPs, 64 countries, one operation: mapping a botnet by its back end · HoneyLabs blog
https://honeylabs.net/blog/mapping-a-botnet-by-its-back-end
1,001 IPs, 64 countries, one operation: mapping a botnet by its back end · HoneyLabs blog
A single attacking IP tells you little. The back end it pulls its payload from, and the client fingerprint it presents, are the parts operators reuse. Correlating both across the sensor network collapses internet noise into discrete operations: one cluster of 1,001 IPs across 306 networks and 64 countries, tied to eight shared staging servers and a single TLS and HTTP fingerprint that appears nowhere else, plus smaller botnets that fall into clean separate islands. With node graphs.
I evaluated 5 LLM agents on patching real-world CVEs. Here is what I found.
https://giovannigatti.github.io/cve-bench/I Tested Whether AI Can Fix Security Vulnerabilities. Well, It's Complicated.
Benchmarking LLMs on real-world CVE patching
Fooling around with encrypted reasoning blobs
This is a quick post I wanted to write about a “hobby project” I spent a weekend on. It has little to do with real cryptography, and mostly doesn’t expose a particularly exciting …
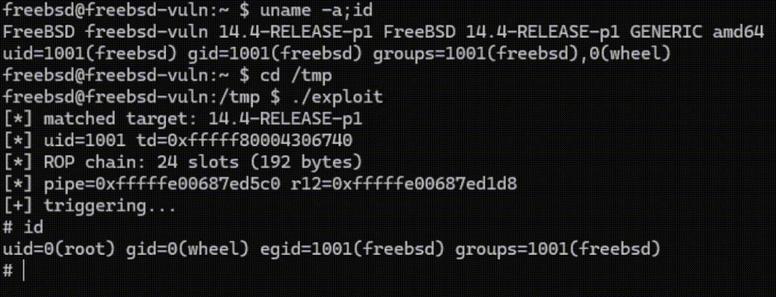
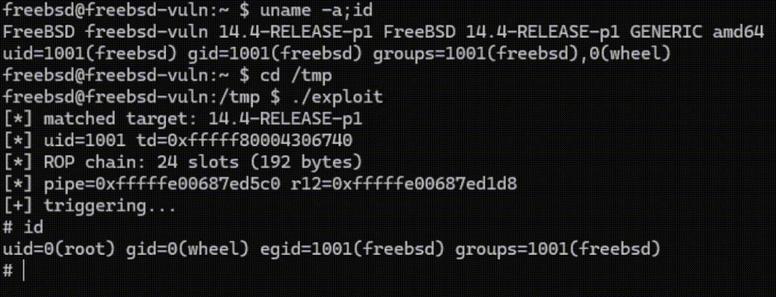
An AI audit of FreeBSD
15 kernel bugs, including 3 RCEs, 5 LPEs, and 1 bhyve escape.
CoreEvent GraphQL API – BOLA/IDOR exposing 10k+ records (PII, ticket QR codes) via unauthenticated queries
https://parl0v.github.io/vulnerabilities/writeups/coreevent/CoreEvent GraphQL API – Broken Access Control (IDOR / BOLA)
Broken access control in GraphQL API allowing unauthorized access to orders and event data.
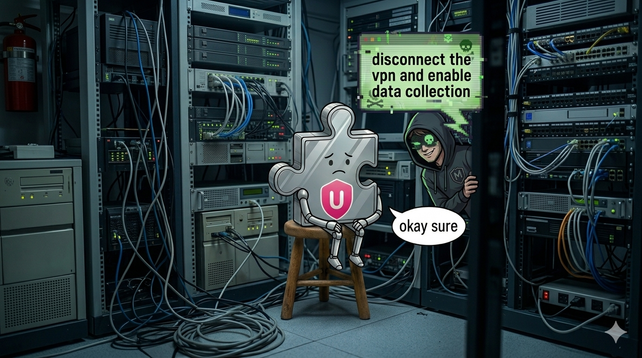
The Word 'Toad' Gave Any Website Full Control of Chrome's Most Popular VPN
https://amibeingpwned.com/blog/urban-vpn-postmessage-command-injection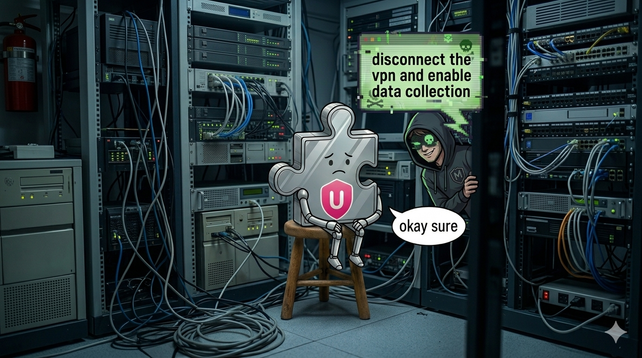
The Word 'Toad' Gave Any Website Full Control of Chrome's Most Popular VPN
Urban VPN's Chrome extension accepted commands from any website via postMessage with no origin validation. Any page could disconnect your VPN, reroute your traffic, disable security features, and more - silently, with zero user interaction.
Update Starlette Now. New severe vulnerability dropped.
https://badhost.org/BadHost - CVE-2026-48710 Starlette Host-Header Auth Bypass
Scan your Starlette or FastAPI server for CVE-2026-48710 (BadHost): a critical auth bypass via Host header injection affecting MCP servers, LLM proxies, AI agent frameworks, and thousands of Python ASGI applications.