Downloading symbols for .exe files is easy with tools like symchk, Windbg, IDA or Ghidra. But how to do it manually, for example on Linux with only few tools available?
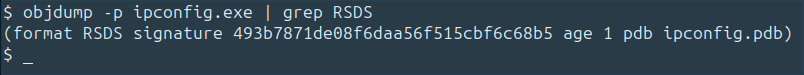
First we need the UUID of the PDB and its age. We could use objdump for this (screenshot).
The info we are getting from running this command (if .exe was compiled with symbols) is all we need to construct the URL: Name of the PDB (in this example ipconfig.pdb), UUID and age:
wget https://msdl.microsoft.com/download/symbols/ipconfig.pdb/493b7871de08f6daa56f515cbf6c68b51/ipconfig.pdb
Please note that the last digit, 2, behind the UUID corresponds to the age value. That's it, the symbols are going to be downloaded.
#reverseengineering