RE: https://infosec.exchange/@briankrebs/116619211861422630
Ayrey said CISA still hadn’t invalidated an RSA private key exposed in the Private-CISA repo that granted access to a GitHub app which is owned by the CISA enterprise account and installed on the CISA-IT GitHub organization with full access to all code repositories.
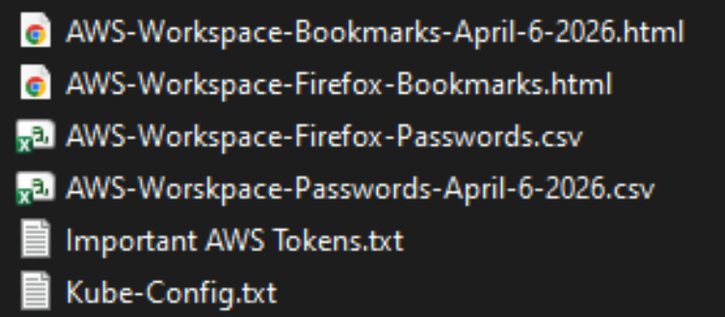
Pure. Unadulterated. Incompetence.