🚨Malware distributed via Steam
Fancy a bit of after work gaming? Beware of infostealer malware distributed via the Steam store!
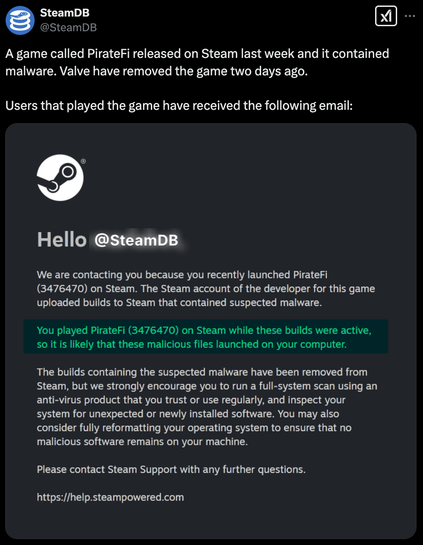
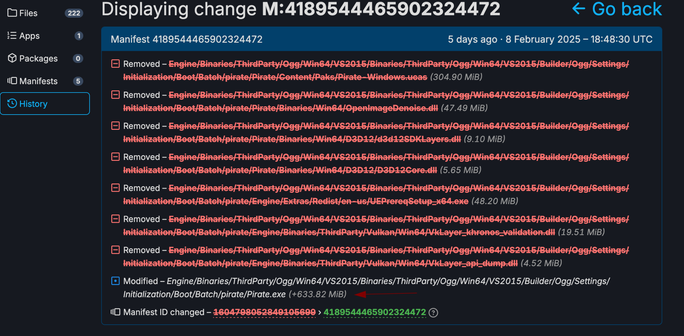
Using @SteamDB we managed to visually identify a very suspicious file in the game files. Luckily, we managed to retrieve a sample for analysis, which will follow in this thread.
The game, which was aptly named "PirateFi", was supposedly Free-to-Play and included web3 / blockchain references, likely as a lure for this specific player base. Steam removed the game from its store yesterday. Approximately 800 to 1500 users have reportedly downloaded PirateFi.
🆘 If you are one of the players who downloaded this "game": Consider the credentials, session cookies and secrets saved in your browser, email client, cryptocurrency wallets etc. compromised. Change passwords for all affected accounts and use Multi-Factor-Authentication where possible. The "game" files will have to be removed from your computer (Steam Libary, %Temp%).
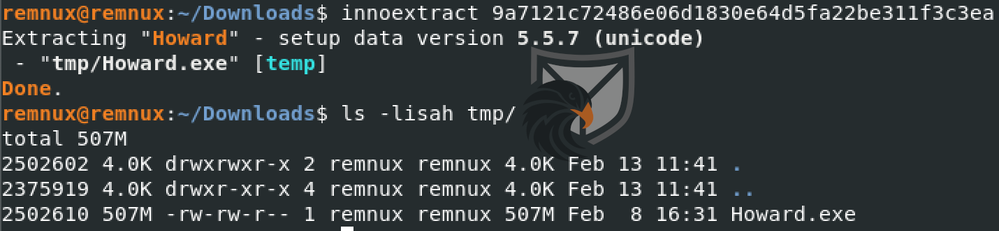
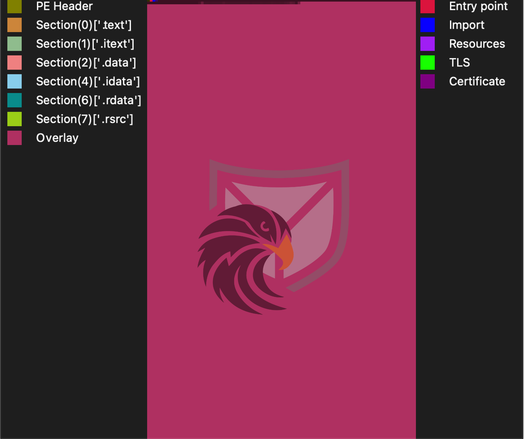
Now onto the malware analysis. The sample of "Pirate.exe" that we managed to dig up is 693MB in size. This property is commonly found with infostealer malware as a low-effort aporach to detection evasion by Anti-Virus and sandboxes. We found that the file contains an InnoSetup installer, which we will have to unpack.