Today: Detecting the "qBit Stealer" exfiltration tool
qBit Stealer was developed by the "qBit #Ransomware-as-a-Service" group to exfiltrate victim data to the MEGA file sharing service. It is implemented in #Golang.
About two months ago the source code of qBit Stealer was published on BreachForums for anyone to use and repurpose (Image 1).
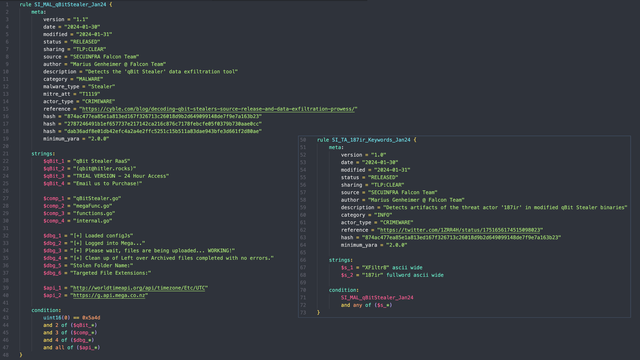
Based on the source code and the sample shared by @1ZRR4H (https://twitter.com/1ZRR4H/status/1751656174515098023), we created a YARA rule to look for qBit Stealer samples (Image 2).
Interestingly, most of the in-the-wild samples contain build artifacts of the "XFiltr8" variant, compiled by a user named "187ir".
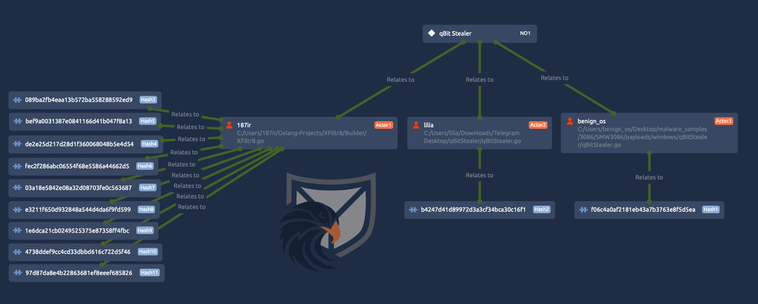
We only found two other public samples that contain different path artifacts (Image 3).
Paths and hashes:
C:/Users/187ir/Golang-Projects/XFiltr8/Builder/XFiltr8.go
089ba2fb4eaa13b572ba558288592ed9
de2e25d217d28d1f360068048b5e4d54
bef9a0031387e0841166d41b047f8a13
fec2f286abc06554f68e5586a44662d5
03a18e5842e08a32d08703fe0c563687
e3211f650d932848a544d4da6f9fd599
1e6dca21cb0249525375e87358ff4fbc
4738ddef9cc4cd33dbbd616c722d5f46
97d87da8e4b22863681ef8eeef685826
C:/Users/benign_os/Desktop/malware_samples/3086/SMW3086/payloads/windows/qBitStealer/qBitStealer.go
f06c4a0af2181eb43a7b3763e8f5d5ea
C:/Users/lilia/Downloads/Telegram Desktop/qBitStealer/qBitStealer.go
b4247d41d89972d3a3cf34bca30c16f1
Samples will be shared via @abuse_ch Malware Bazar
The rules will be pushed to the 100DaysOfYARA and our detection repo :)
🍪
Germán Fernández (@1ZRR4H) on X
#opendir https://91.92.254.14/ "XFiltr8.exe" appears to be an exfiltration tool (written in Go) that uses MEGA services for storage via g.api.mega.]co.]nz. [+] https://t.co/T3dWYx5Elk ▪ "C:/Users/187ir/Golang-Projects/XFiltr8/Builder/XFiltr8.go" "Helpertask.exe" is #AsyncRAT…