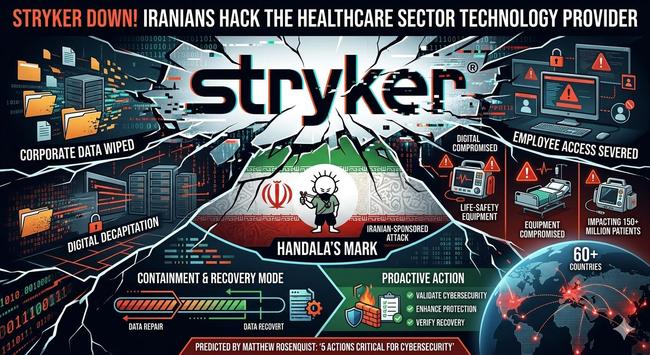
Stryker, a major medical equipment provider for the healthcare sector, has suffered a destructive cyberattack that wiped corporate data and severed employee access, likely from an Iranian sponsored hacking group.
Stryker Corporation is a global leader in medical technology, with over $22 billion in sales and 53 thousand employees. The company provides critical healthcare equipment and solutions to hospitals, fire departments, paramedics, and medical facilities worldwide.
Healthcare is a critical infrastructure sector and Stryker is a prominent supplier of life-safety equipment in over 60 countries, impacting more than 150 million patients according to their website.
The attack appears to have been a digital decapitation hack, at the administrator access-level, that wiped internal systems data, including corporate endpoint devices and phones.
Full Story on my Substack: https://matthewrosenquist.substack.com/p/stryker-down-iranians-hack-the-healthcare
#cybersecurity #hack