@LostAmishMan
- 0 Followers
- 16 Following
- 8 Posts
Aegis Core S.O.S. , evidence in hand: APT, supply chain & persistent rootkit ops.
Seeking OSINT, blue/gray hats to review, collaborate, or amplify. Not for tourists—if you’ve stared down real evil, we want you.
DM to join or see the data.
Thank you in Advance. Again, please know your sh*t.
Action Steps:
Monitor all outbound PKI cert traffic to DoD/DISA and volume spikes—especially on non-admin systems.
Dump & hash all current root/intermediate certs.
Verify your “trusted roots” against air-gapped, known-good images.
Don’t trust “automated recovery” if you notice PKI/OCSP anomalies.
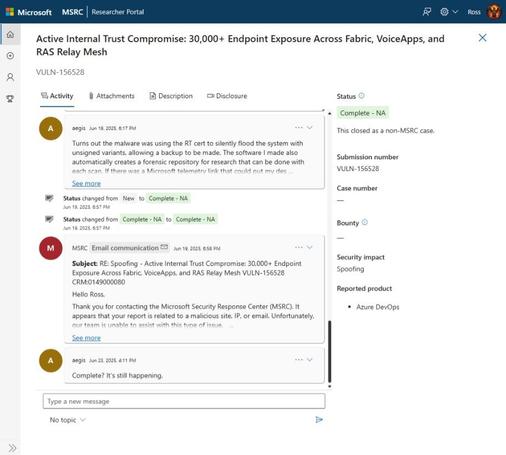
We are witnessing the weaponization of certificate trust infrastructure against military/civilian defense.
#infosec #DoD #PKI #cybersecurity #zerotrust #supplychain #nationalsecurity
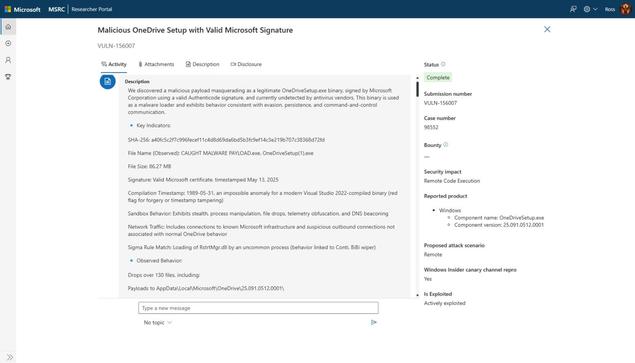
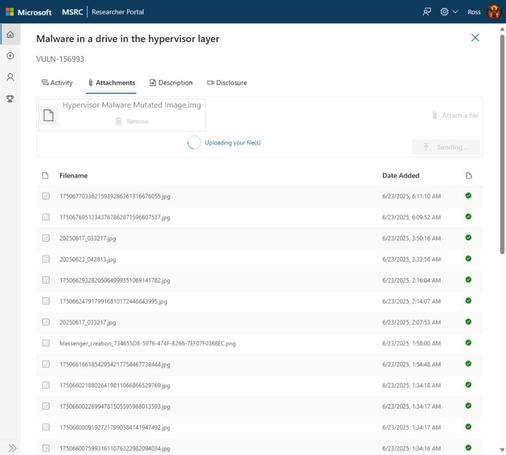
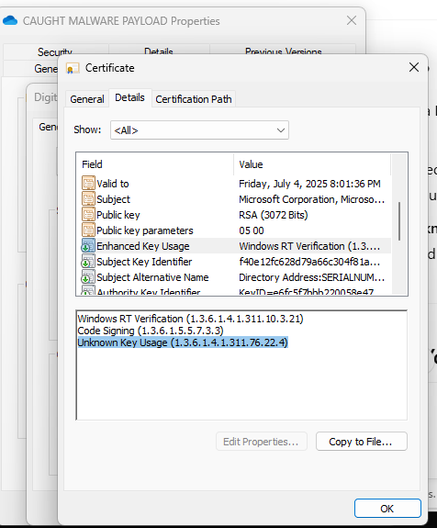
We have confirmed evidence of a hypervisor-level implant generating synthetic certificates and mass-downloading new certs from DISA (DoD PKI) daily using bot networks.
Thousands of requests per day—way above any legit operational use.
Cert expiry is being used as a potential kill switch or command signal.
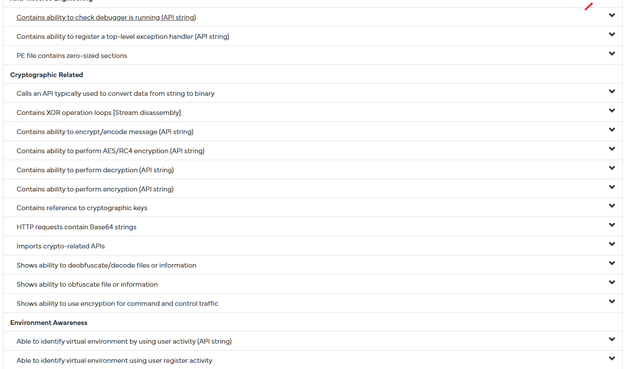
This operation is embedded below the OS layer—can survive reinstalls, hides as legitimate system activity, and pivots via OneDrive, MS cloud, & telemetry endpoints.
Ever see a hypervisor malware written in MSDOS 5.0?
Ok, ever see one that hijacks the boot and jumps into UEFI shell to communicate with and feed Defender signed V 0.0 certs? Whoever wrote this knows DOS and how to trip up scanning.
If you'd like to help take it apart, shoot me a DM. No tourists please, if you know anything about airgapped DoD or Blacksite machines, this will be the thing you talk about for years to come.
Aegis Core S.O.S. , evidence in hand: APT, supply chain & persistent rootkit ops.
Seeking OSINT, blue/gray hats to review, collaborate, or amplify. Not for tourists—if you’ve stared down real evil, we want you.
DM to join or see the data.
Thank you in Advance. Again, please know your sh*t.