I'm just this guy, you know!
- Views my own 😇
- Security Advisor @ Reykur.io 👔
- ex-Staff Security dino @ Google 🦕
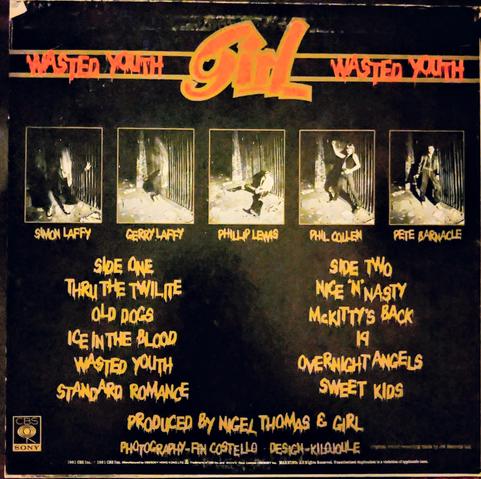
- Purveyor of fine whisky 🥃, hard mixes 🎧🎚️, & fresh bull 💩
- Zurich 🇨🇭 / Valencia 🇪🇸
- FI/RE
DJ Mixes https://mixcloud.com/c22dnb #dnb #DrumAndBass
| Twitter :twitter: | https://twitter.com/intent/user?screen_name=ChrisJohnRiley |
| Blog ✍️ | https://blog.c22.cc |
| GitHub :github: | https://github.com/ChrisJohnRiley |