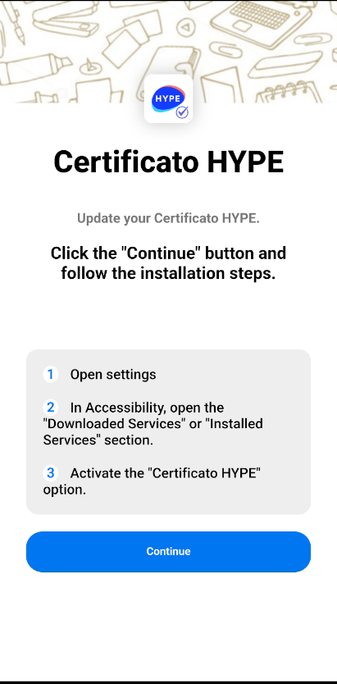
Italian 🇮🇹 bank Widiba is the latest victim of Copybara impersonation. Newer variants also now implement anti-debug checks to prevent running on an emulator. Some more variants impersonating an ISP and the Poste can be seen at an open directory.
C2 : 45.86.231[.]15
Technical analysis here : https://www.zscaler.com/blogs/security-research/technical-analysis-copybara
Ruchna 
- 8 Followers
- 47 Following
- 14 Posts
C2 : 92.255.85[.]200
#Android #Malware
Noticed an <activity-alias> definition in an AndroidManifest.xml for the first time and this particular case specifies android:enabled as false for the alias. Truly curious why an application (malicious in this case) would define an activity-alias if it didn't want for it to be instantiated?
LightSpy2 feature rich mobile surveillance tool set - Victor Chebyshev
From ERMAC to Hook: Investigating the technical differences between two Android malware variants
Authored by Joshua Kamp (main author) and Alberto Segura. Summary Hook and ERMAC are Android based malware families that are both advertised by the actor named “DukeEugene”. Hook is the latest vari…
From Google DNS to Tech Support Scam Sites: Unmasking the Malware Trail
Bad actors are elevating their malware campaigns by leveraging the DNS protocol to hide requests to their infrastructure. Learn how hackers are injecting malicious JavaScript to send requests to Google DNS, then using the responses to redirect users to tech support scams and adult websites.