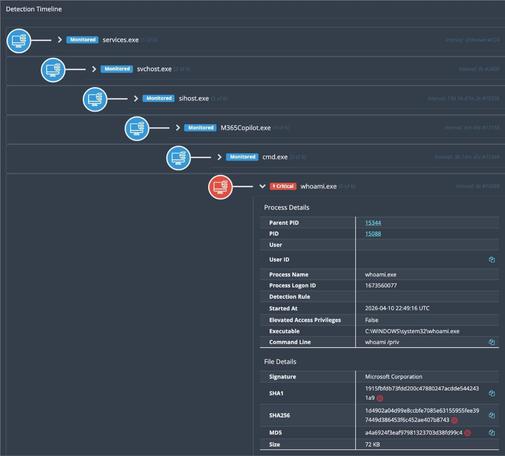
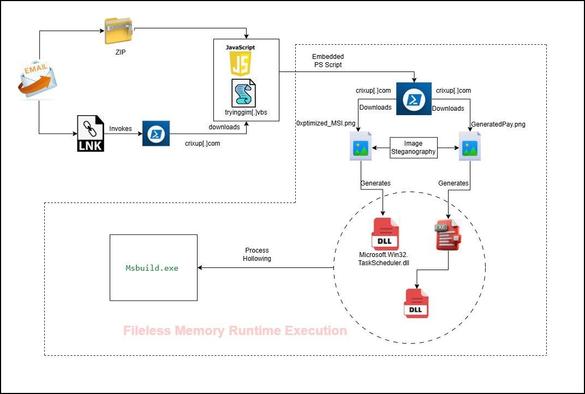
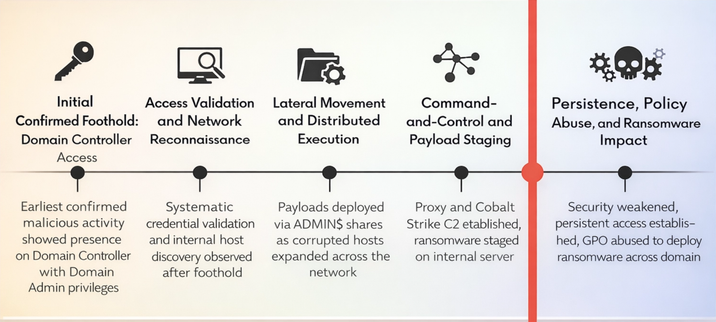
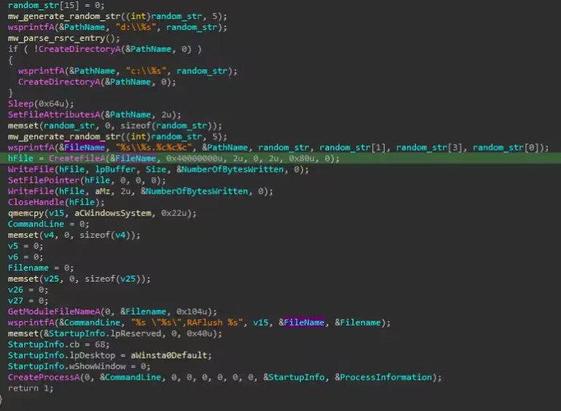
Huntress researchers Anna Pham & Michael Tigges write about having observed the use of Nightmare-Eclipse tooling - including BlueHammer, RedSun and UnDefend - during a real-world intrusion investigation. https://www.huntress.com/blog/nightmare-eclipse-intrusion
Organisers of the annual Virus Bulletin conference.