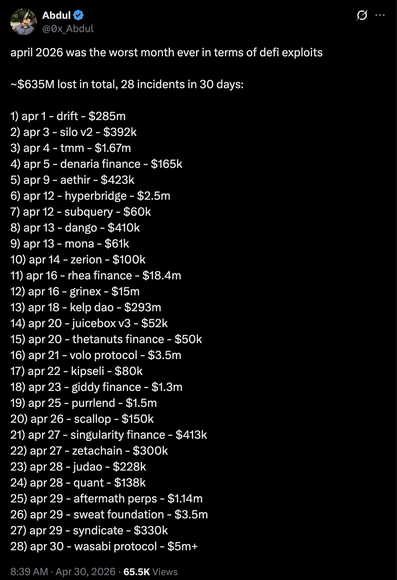
📰 Lazarus Group Unleashes 'RemotePE' Memory-Only RAT in Attacks on Financial and Crypto Firms
🇰🇵 Lazarus Group deploys new 'RemotePE' memory-only RAT against financial & crypto firms. The fileless malware evades detection by never touching the disk, using a multi-stage infection chain. #LazarusGroup #Malware #ThreatIntel #RemotePE
🌐 cyber[.]netsecops[.]io