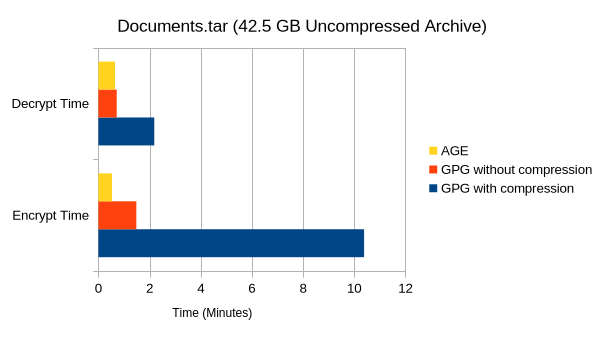
So I think moving forward I'm switching to #AGE for file #encryption instead of #PGP. I occasionally make backup archives of various things and use passphrase encryption with #GPG to encrypt them before storing them. However, GPG is very slow for bigger files, and in some testing recently I discovered AGE is multiple times faster. Also, with their latest release they now support hybrid post #quantum assymmetric key pairs. So for encryption it can fully replace GPG.
So it seems that at least part of the slow-down I experienced with #GPG is because, by default, it gzip compresses the encrypted files. This can be disabled in the command line if you're encrypting an already compressed archive for pretty substantial improvements in encrypt/decrypt speeds. AGE was still faster, but nearly as much.
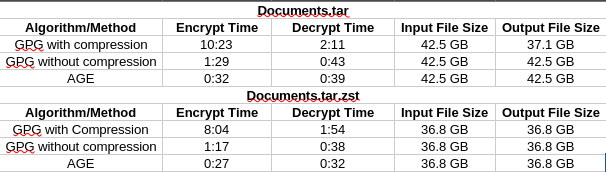
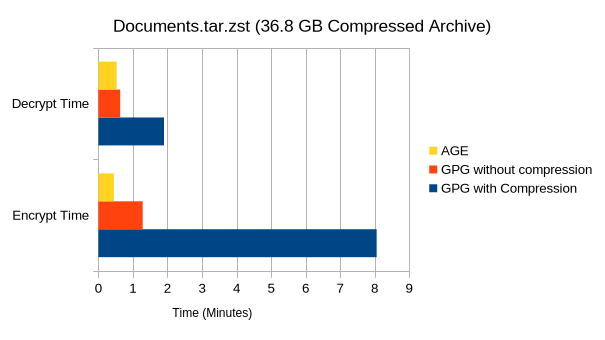
On a large zst (38.9 GB) archive of my Documents folder, here's some encrypt times.
AGE: 0:28
GPG (w/ compression): 8:12
GPG (w/o compression): 1:19
@upofadown I finished writing everything down and have posted it here. GPG, as far as I can tell, doesn't explicitly tell you what mode it's using. All I ever see it say is "AES256", though I believe it defaults to CFB these days. I'm not a cryptographer though, so you can probably glean more information than I just by looking at my setup and results.
Link: https://open.substack.com/pub/gerowen/p/age-vs-gpg-pgp-encryption
@gerowen You can apparently force OCB on. So:
gpg --force-ocb --no-compress -c totc.txt
I used pgpdump to look at the result and it said the mode was 20, which sounds right for GPG OCB. GPG should really let you know what mode you are using as there are now different non-interoperable versions of OCB around due to the standards schism.
I found it interesting that GPG encryption took longer than GPG decryption. CFB mode doesn't parallelize for encryption but can be done in parallel for decryption. I wonder if that is coming out here. Having something better than CFB mode for performance is an important reason OCB mode exists.
@upofadown And yes, the CPU has hardware accelerated AES instruction sets available, and listed in /proc/cpuinfo.
https://www.amd.com/en/products/processors/laptop/ryzen/8000-series/amd-ryzen-9-8945hs.html