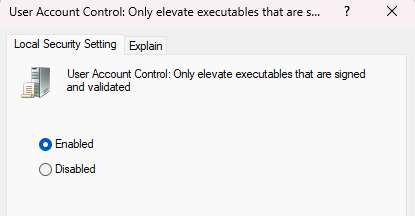
can someone explain to me the point of this security policy
like what kind of problem is this trying to solve when there are 5 million other signed system executables capable of proxy execution
That is a bit of a strange one as UAC is not a security boundary, allegedly.
Microsoft change their minds on that one as the mood suits though 🤔🤷♂️
@still Tame the devs and sysadmins to go through signing process for edr allowlisting.But yeah... it's not a true security boundary. Just a way to channel supply chain into compliance.