> new sample
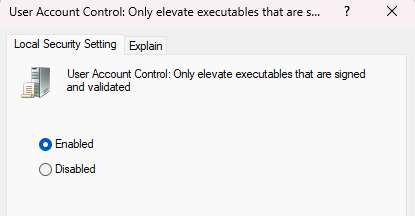
> 300kb+ for the loader
> the loader is filled with millions of jump tables and CFFs
> "but ok it's just ReadFile and NtAllocateVirtualMemory I can deal with that at runtime"
> realizes I've got over dozens of similar loaders to analyze
> I need to automate this
> LLMs can't be bothered with identifying the decrypting logic due to large amounts of CFFs
> speakeasy breaks because it's speakeasy
alright chat if anyone needs me I'll be crying myself to bed