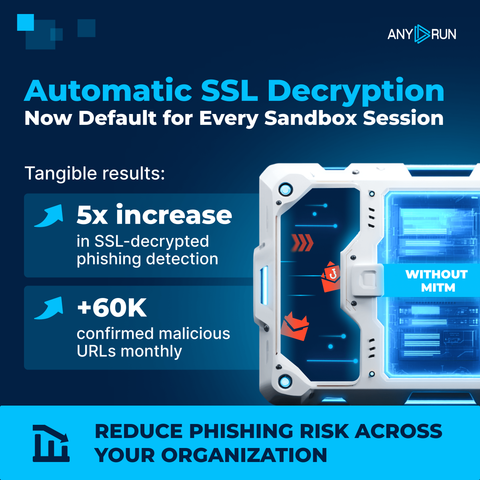
⚠️ Encrypted HTTPS traffic remains one of the main reasons #phishing is harder to confirm quickly. Automatic SSL decryption significantly expands visibility in every #ANYRUN Sandbox session. See real-world examples:
🔹 #EvilTokens. Decrypted traffic exposed hidden HTTPS API calls behind the OAuth Device Code phishing flow, revealing session control and attacker infrastructure: https://app.any.run/tasks/2e8014a8-a90a-41bf-90fa-aa65da40fd20/?utm_source=mastodon&utm_medium=post&utm_campaign=ssl_decryption_examples&utm_term=020426&utm_content=linktoservice
🔹#FlowerStorm. SSL decryption enabled early detection of this phishkit via POST requests to /google.php at initial page load, before any user interaction or data entry: https://app.any.run/tasks/25694db7-2771-480c-9ff0-773e399331d6/?utm_source=mastodon&utm_medium=post&utm_campaign=ssl_decryption_examples&utm_term=020426&utm_content=linktoservice
🔹 Phishing via Telegram API. Decrypted traffic revealed data exfiltration through the Telegram Bot API, helping identify localized campaigns via encrypted traffic patterns: https://app.any.run/tasks/49484bb5-28ec-44ca-835a-9b3235bd6419/?utm_source=mastodon&utm_medium=post&utm_campaign=ssl_decryption_examples&utm_term=020426&utm_content=linktoservice
⚡️ Reduce phishing risk across your organization. Integrate #ANYRUN into your SOC’s triage & response workflows: https://any.run/enterprise/?utm_source=mastodon&utm_medium=post&utm_campaign=ssl_decryption_examples&utm_term=020426&utm_content=linktoenterpriselanding