Local File Inclusion in a PHP Reservation System — From Parameter Abuse to Source Code Disclosure
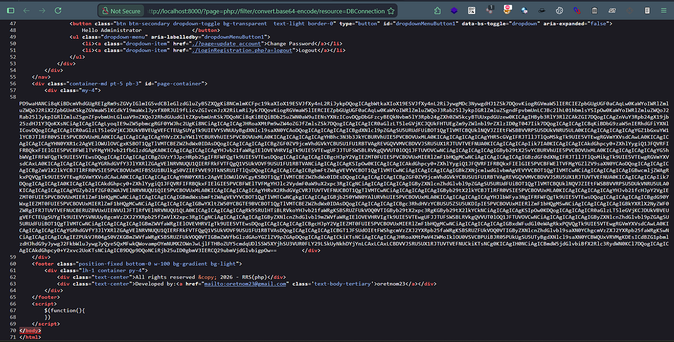
This vulnerability was a Local File Inclusion (LFI) in a PHP reservation system due to insufficient input validation on user-controlled parameters. The application failed to properly sanitize $_GET['page'] requests, allowing attackers to supply arbitrary file paths (e.g., '../config.php') for inclusion within the page content. By crafting payloads that leveraged this flaw, such as 'index.php?page=../../config.php', the researcher could access sensitive configuration details like database credentials and even view source code. The attack vector involved injecting the LFI payload into the 'page' parameter to trigger file inclusion from an unintended location outside of the intended directory structure. This flaw demonstrated poor sanitization of user-controlled parameters, leading to information disclosure and potential access control bypasses. The attacker received $5,000 for reporting the vulnerability. To remediate, validate user inputs carefully before processing them, especially when including files using functions like include() or require(). Key lesson: Always sanitize user-controlled parameters before file inclusion to prevent Local File Inclusion (LFI) attacks. #BugBounty #Cybersecurity #WebSecurity #InputSanitization #LocalFileInclusion