Proofpoint has directly observed a targeted email campaign that delivers DarkSword RCE, and we attribute the messages to Russian FSB threat actor TA446 with high confidence. We have not previously observed TA446 target users’ iCloud accounts or Apple devices, but the adoption of the leaked DarkSword iOS exploit kit has now enabled the actor to target iOS devices. TA446 does not overlap with UNC6353.
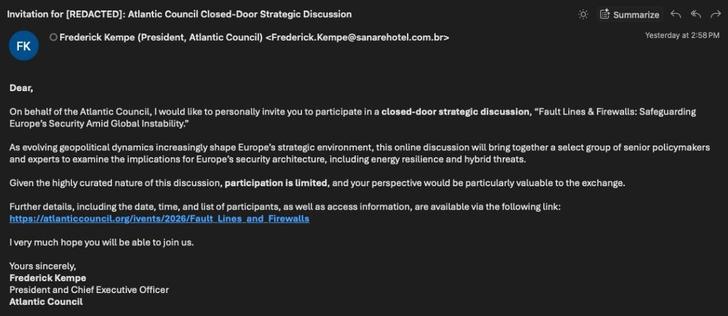
On March 26, 2026, Proofpoint observed many compromised senders spoofing the Atlantic Council in a campaign that we attribute to TA446 (Callisto, COLDRIVER, Star Blizzard, which is linked to Russia’s FSB Centre 18). The volume of emails from TA446 has been significantly higher over the last 2 weeks compared to normal operational tempo delivering the MAYBEROBOT backdoor via password-protected ZIP files. The activity on March 26 was a similar spike, but with links instead of attachments. Proofpoint automated analysis was redirected to a benign decoy PDF, likely because of server-side filtering to only redirect iPhone browsers to the exploit kit.
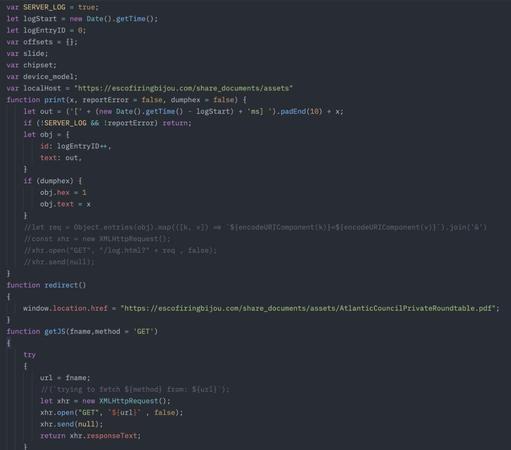
New reports on TA446 using the DarkSword iOS exploit kit were intriguing. The DarkSword iOS exploit kit was recently published on GitHub, but Proofpoint had not yet observed it in use in the wild. A DarkSword loader uploaded to VirusTotal (MD5: 5fa967dbef026679212f1a6ffa68d575) referenced escofiringbijou[.]com, a TA446 second-stage domain independently observed by Proofpoint, corroborating the group's use of DarkSword.
A submission on URLScan (https://urlscan.io/result/019d2c02-e06f-773f-a7a8-72516045f0da/#transactions) confirmed that the TA446-controlled domain was serving the DarkSword exploit kit, including the initial redirector, exploit loader, RCE, and PAC bypass components. The sandbox escapes were not observed.
Related compromised first stage domains also include motorbeylimited[.]com and bridetvstreaming[.]org. Only the activity from March 26 spoofing Atlantic Council has been linked to DarkSword usage; previous TA446 activity shows no indication of exploit use.
Proofpoint did not directly observe the iOS exploit kit delivery but believe the actor has adopted the exploit kit for the purposes of credential harvesting and intelligence collection. The targeting Proofpoint observed in the email campaigns was much wider than usual and included government, think tank, higher education, financial, and legal entities, indicating that this new capability led TA446 to attempt to use DarkSword opportunistically against a broader target set. This is a notable adoption, as Proofpoint has not previously observed TA446 targeting iOS devices.