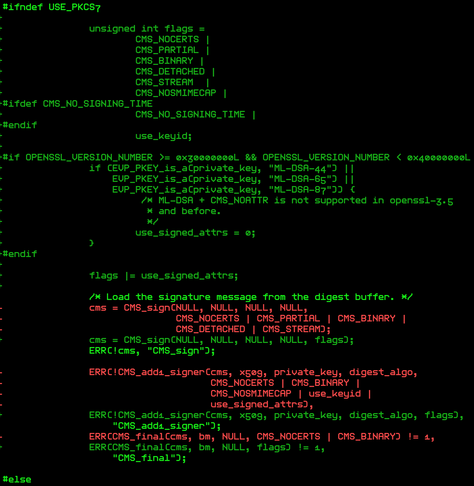
so of course i was like:
Waive rejection of authenticatedAttributes for ML-DSA (PKCS7_WAIVE_AUTHATTRS_REJECTION_FOR_MLDSA) [N/y/?] (NEW) n
ok
crypto/asymmetric_keys/Kconfig
47-config PKCS7_MESSAGE_PARSER
48- tristate "PKCS#7 message parser"
49- depends on X509_CERTIFICATE_PARSER
50- select CRYPTO_HASH
51- select ASN1
52- select OID_REGISTRY
53- help
54- This option provides support for parsing PKCS#7 format messages for
55- signature data and provides the ability to verify the signature.
56-
57:config PKCS7_WAIVE_AUTHATTRS_REJECTION_FOR_MLDSA
58- bool "Waive rejection of authenticatedAttributes for ML-DSA"
59- depends on PKCS7_MESSAGE_PARSER
60- depends on CRYPTO_MLDSA
61- help
62- Due to use of CMS_NOATTR with ML-DSA not being supported in
63- OpenSSL < 4.0 (and thus any released version), enabling this
64- allows authenticatedAttributes to be used with ML-DSA for
65- module signing. Use of authenticatedAttributes in this
66- context is normally rejected.
67-
crypto/asymmetric_keys/pkcs7_parser.c
85- */
86-static int pkcs7_check_authattrs(struct pkcs7_message *msg)
87-{
88- struct pkcs7_signed_info *sinfo;
89- bool want = false;
90-
91- sinfo = msg->signed_infos;
92- if (!sinfo)
93- goto inconsistent;
94-
95:#ifdef CONFIG_PKCS7_WAIVE_AUTHATTRS_REJECTION_FOR_MLDSA
96- msg->authattrs_rej_waivable = true;
97-#endif
98-
99- if (sinfo->authattrs) {
100- want = true;
101- msg->have_authattrs = true;
102:#ifdef CONFIG_PKCS7_WAIVE_AUTHATTRS_REJECTION_FOR_MLDSA
103- if (strncmp(sinfo->sig->pkey_algo, "mldsa", 5) != 0)
104- msg->authattrs_rej_waivable = false;
105-#endif
106- } else if (sinfo->sig->algo_takes_data) {
107- sinfo->sig->hash_algo = "none";
108- }
109-
110- for (sinfo = sinfo->next; sinfo; sinfo = sinfo->next) {
111- if (!!sinfo->authattrs != want)
112- goto inconsistent;