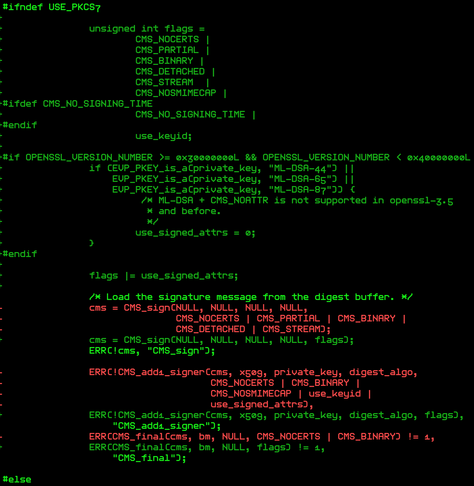
didn't post this earlier but this is what it looks like if you happened to pull master randomly this week like i did (keyword ML-DSA)
*
* Public-key cryptography
*
RSA (Rivest-Shamir-Adleman) (CRYPTO_RSA) [Y/?] y
DH (Diffie-Hellman) (CRYPTO_DH) [Y/?] y
RFC 7919 FFDHE groups (CRYPTO_DH_RFC7919_GROUPS) [Y/n/?] y
ECDH (Elliptic Curve Diffie-Hellman) (CRYPTO_ECDH) [Y/?] y
ECDSA (Elliptic Curve Digital Signature Algorithm) (CRYPTO_ECDSA) [Y/?] y
EC-RDSA (Elliptic Curve Russian Digital Signature Algorithm) (CRYPTO_ECRDSA) [M/n/y/?] m
ML-DSA (Module-Lattice-Based Digital Signature Algorithm) (CRYPTO_MLDSA) [N/m/y/?] (NEW) y
*
* Asymmetric (public-key cryptographic) key type
*
Asymmetric (public-key cryptographic) key type (ASYMMETRIC_KEY_TYPE) [Y/?] y
Asymmetric public-key crypto algorithm subtype (ASYMMETRIC_PUBLIC_KEY_SUBTYPE) [Y/?] y
X.509 certificate parser (X509_CERTIFICATE_PARSER) [Y/?] y
PKCS#8 private key parser (PKCS8_PRIVATE_KEY_PARSER) [M/n/y/?] m
PKCS#7 message parser (PKCS7_MESSAGE_PARSER) [Y/?] y
Waive rejection of authenticatedAttributes for ML-DSA (PKCS7_WAIVE_AUTHATTRS_REJECTION_FOR_MLDSA) [N/y/?] (NEW) n
PKCS#7 testing key type (PKCS7_TEST_KEY) [N/m/y/?] n
Support for PE file signature verification (SIGNED_PE_FILE_VERIFICATION) [Y/n/?] y
Run FIPS selftests on the X.509+PKCS7 signature verification (FIPS_SIGNATURE_SELFTEST) [N/m/y/?] n
*
* Certificates for signature checking
*
File name or PKCS#11 URI of module signing key (MODULE_SIG_KEY) [certs/signing_key.pem] certs/signing_key.pem
Type of module signing key to be generated
1. RSA (MODULE_SIG_KEY_TYPE_RSA)
> 2. ECDSA (MODULE_SIG_KEY_TYPE_ECDSA)
3. ML-DSA-44 (MODULE_SIG_KEY_TYPE_MLDSA_44) (NEW)
4. ML-DSA-65 (MODULE_SIG_KEY_TYPE_MLDSA_65) (NEW)
5. ML-DSA-87 (MODULE_SIG_KEY_TYPE_MLDSA_87) (NEW)
choice[1-5?]: 2
Provide system-wide ring of trusted keys (SYSTEM_TRUSTED_KEYRING) [Y/?] y
Additional X.509 keys for default system keyring (SYSTEM_TRUSTED_KEYS) []
Reserve area for inserting a certificate without recompiling (SYSTEM_EXTRA_CERTIFICATE) [N/y/?] n
Provide a keyring to which extra trustable keys may be added (SECONDARY_TRUSTED_KEYRING) [Y/n/?] y
Only allow additional certs signed by keys on the builtin trusted keyring (SECONDARY_TRUSTED_KEYRING_SIGNED_BY_BUILTIN) [N/y/?] n
Provide system-wide ring of blacklisted keys (SYSTEM_BLACKLIST_KEYRING) [Y/n/?] y
Hashes to be preloaded into the system blacklist keyring (SYSTEM_BLACKLIST_HASH_LIST) []
Provide system-wide ring of revocation certificates (SYSTEM_REVOCATION_LIST) [Y/n/?] y
X.509 certificates to be preloaded into the system blacklist keyring (SYSTEM_REVOCATION_KEYS) []
Allow root to add signed blacklist keys (SYSTEM_BLACKLIST_AUTH_UPDATE) [Y/n/?] y