whatever. anyway you read the commit messages
modsign: Enable ML-DSA module signing
Allow ML-DSA module signing to be enabled.
don't care but ok. "allow". "enable". "allow to be enabled" whatever quantum is fake
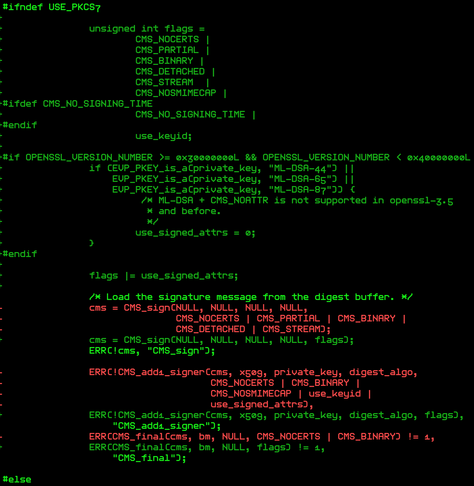
Note that OpenSSL's CMS_*() function suite does not, as of OpenSSL-3.6,
support the use of CMS_NOATTR with ML-DSA, so the prohibition against using
signedAttrs with module signing has to be removed. The selected digest
then applies only to the algorithm used to calculate the digest stored in
the messageDigest attribute. The OpenSSL development branch has patches
applied that fix this[1], but it appears that that will only be available
in OpenSSL-4.
good documentation of version compat, ok
[1] https://github.com/openssl/openssl/pull/28923
sign-file won't set CMS_NOATTR if openssl is earlier than v4, resulting in
the use of signed attributes.
The ML-DSA algorithm takes the raw data to be signed without regard to what
digest algorithm is specified in the CMS message. The CMS specified digest
algorithm is ignored unless signedAttrs are used; in such a case, only
SHA512 is permitted.
this is complete word salad. that's a huge red flag
...
maybe fine for a dev branch but they are on master! call coming from inside the house!
git show 0ad9a71933e73c8a2af101d28e9a1dc35bae02d5
[...]
ML-DSA does its own hashing,
spent an hour destroying my brain with this shit
https://nvlpubs.nist.gov/nistpubs/FIPS/NIST.FIPS.204.pdf
it does not "do its own hashing"
In the HashML-DSA version, the message input to ML-DSA.Sign_internal is the result of applying either a hash function or a XOF to the content to be signed.
do they really think they can be more brain destroying than working on build and packaging