| GitHub | https://github.com/ssnkhan |
| Keybase | https://snkhan.keybase.pub/mastodon.html |
| Location | Sheffield, United Kingdom |
Sajid Nawaz Khan 
- 152 Followers
- 476 Following
- 316 Posts
We told employees to "be suspicious" of links they needed for work. Now we're adding "be careful with AI" to the awareness curriculum. Teaching when to escalate works better than teaching what to fear.

Awareness Training Won't Protect Employees from Their Own AI Tools
When an AI tool influences an employee's decision, audit logs record the human's action and miss the AI's role. Addressing that blind spot requires escalation procedures and engineering controls that go beyond what awareness programs can deliver.
The release of ATT&CK v19, expected on 28 April 2026, will split the Defense Evasion tactic into two: Stealth, and Impair Defenses.
As a result of these updates, a number of sub-techniques within T1562 (Impair Defenses) will likely now be promoted to technique level. More details at:
https://medium.com/mitre-attack/defense-evasion-split-a-tale-of-two-tactics-5d533545fa32
I shall never tire of the Barbican.
If you’re a macOS user supporting with Windows digital forensics, you’ll love IRFlow Timeline:
“A high-performance native macOS application for DFIR timeline analysis. Built on Electron + SQLite to handle large files for forensic timelines (CSV, TSV, XLSX, EVTX, Plaso) without breaking a sweat. Inspired by Eric Zimmerman's Timeline Explorer for Windows.”
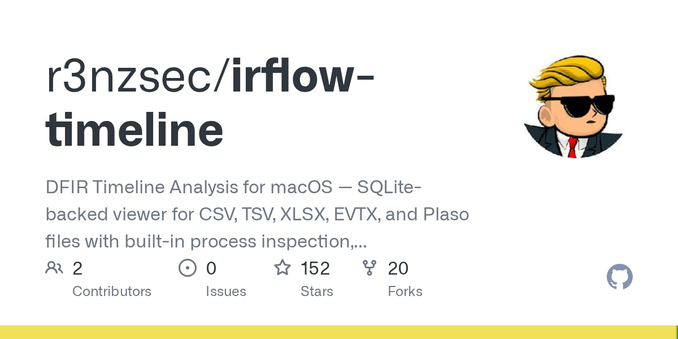
GitHub - r3nzsec/irflow-timeline: DFIR Timeline Analysis for macOS — SQLite-backed viewer for CSV, TSV, XLSX, EVTX, and Plaso files with built-in process inspection, lateral movement tracking, and persistence detection.
DFIR Timeline Analysis for macOS — SQLite-backed viewer for CSV, TSV, XLSX, EVTX, and Plaso files with built-in process inspection, lateral movement tracking, and persistence detection. - r3nzsec/i...
@teamcymru_S2 Hi, can you please include the publishing date on your blog posts please? e.g.,
https://www.team-cymru.com/post/tracking-orbs-on-singapores-telecommunications-networks
The new REMnux MCP server connects AI agents to 200+ malware analysis tools. I was surprised at the depth of investigation it can deliver: https://zeltser.com/ai-malware-analysis-remnux
Most of my time on this project went into capturing how I approach malware analysis and making sure the server provides the right guidance at the right time, so that AI can think and adapt as it creates the workflow. The post includes interactive replays of real analysis sessions.
#malware #malwareanalysis #infosec #cybersecurity #tools #artificialintelligence #AI
Using AI Agents to Analyze Malware on REMnux
To analyze malware effectively, AI agents need practitioners' expertise and access to the analysis tools. The REMnux MCP server provides both, connecting AI to 200+ tools on REMnux with guidance on which to run and how to interpret their output.
A convoluted Lotus Blossom infection chain leads to an otherwise unremarkable Cobalt Strike configuration:
https://www.rapid7.com/blog/post/tr-chrysalis-backdoor-dive-into-lotus-blossoms-toolkit/
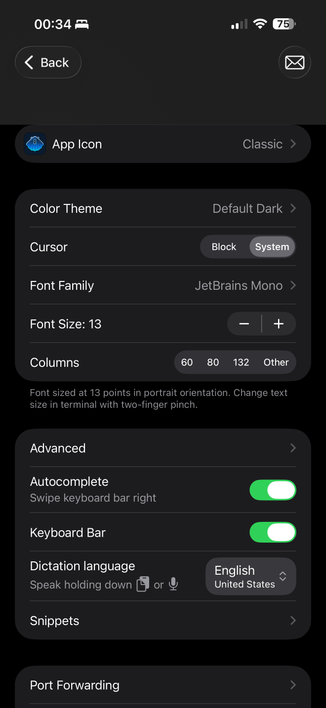
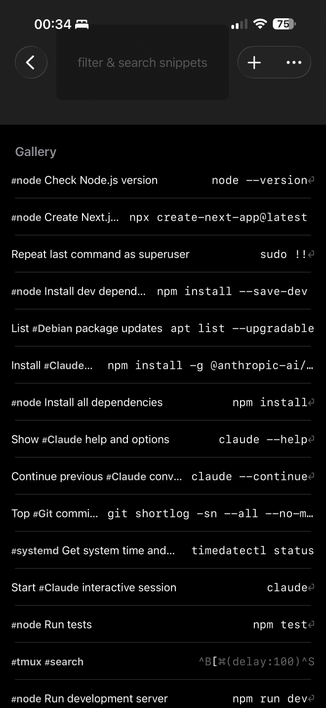
@ShellFish Happy New Year! Found a reproducible bug, which hides the Settings heading label across all areas:
1. Settings
2. Shell Integration (make no changes, then back out to the previous screen)
3. All Titles now missing
This also causes havoc in various places, like in the Snippets page.