You just provisioned a fresh Linux server. Within minutes, the SSH brute-force bots will arrive.
There are too many ways to build a firewall in Linux. I wrote a practical guide to the four major tools: iptables, nftables, firewalld, and ufw, including their mental models and deployable configs.
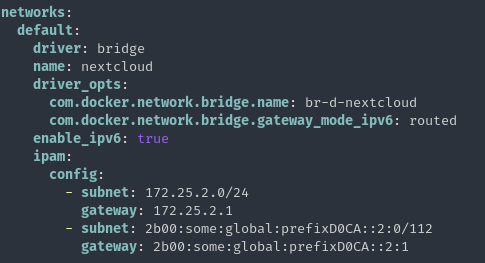
Also includes a deep dive into the "Docker Trap" (why Docker silently bypasses your default-deny rules) and how to fix it.
(And yes, I still spend the intro and conclusion reminding everyone that FreeBSD's PF is the undisputed king of packet filtering. Let's argue in the replies.)
Read it here: https://blog.hofstede.it/linux-firewalls-how-to-actually-secure-a-cloud-server-iptables-nftables-firewalld-ufw/
#Linux #Sysadmin #DevOps #Security #Netfilter #Docker #Networking

Linux Firewalls: How to Actually Secure a Cloud Server (iptables, nftables, firewalld, ufw)
A practical guide to the four major Linux firewall technologies - iptables, nftables, firewalld, and ufw. Covers real-world cloud server hardening with concrete examples, from locking down SSH to b...