RE: https://infosec.exchange/@_r_netsec/116220859869337905
Waah, joli boulot.
Je me demande qui en est l’auteur.
lecture technique très intéressante.
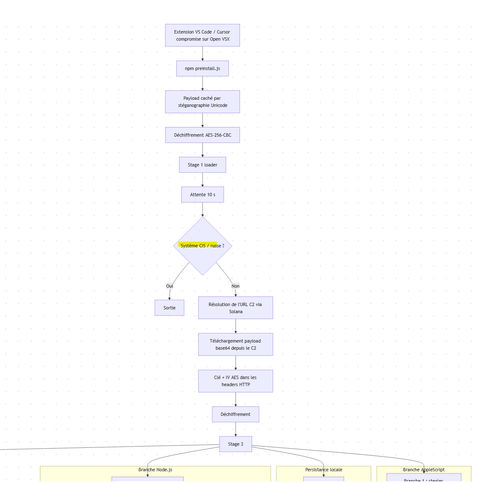
Une analyse statique complétée par du monitoring comportementale réseau qui plonge dans les entrailles du ver infostealer macOS injecté dans un plugin VS Code lors de la campagne Glassworm v2.. 👀
C’est balaise et résilient, avec une belle répartition des tâches de vol entre AppleScript et Node.js. 
Les échantillons déobfusqués ont aussi été mis à disposition sur #malwarebazaar
https://bazaar.abuse.ch/sample/d72c1c75958ad7c68ef2fb2480fa9ebe185e457f3b62047b31565857fa06a51a/
#CyberVeille #MacSecurity #macOS #Malware #ThreatIntel #Glassworm
👇
 decio
decio