CVE-2025-5777 (Citrix Netscaler vuln) has been under active exploitation since mid June, with people dumping memory and using this to try to access sessions.
TTPs to hunt for:
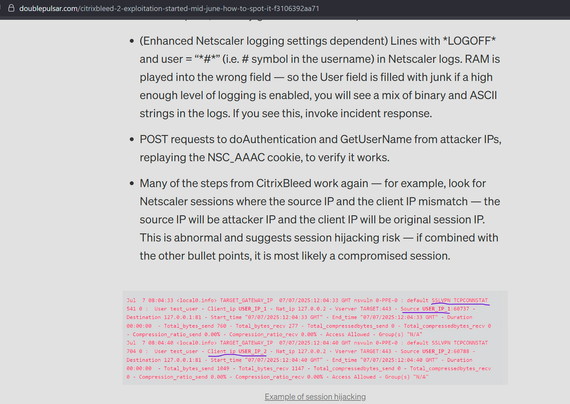
- In Netscaler logs, repeated POST requests to *doAuthentication* - each one yields 126 bytes of RAM
- In Netscaler logs, requests to doAuthentication.do with "Content-Length: 5"
- In Netscaler user logs, lines with *LOGOFF* and user = "*#*" (i.e. # symbol in the username). RAM is played into the wrong field.
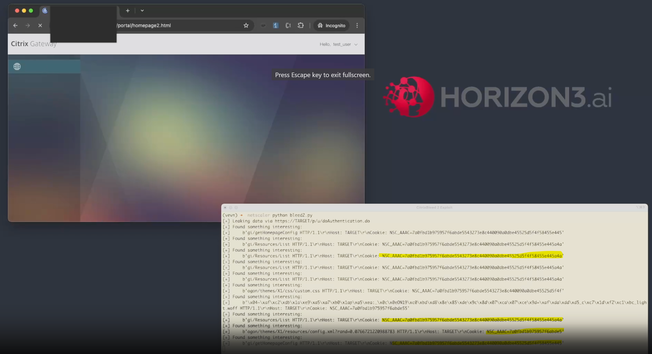
Horizon3 have a good write up here, I don't think they were aware this is already being exploited for almost a month: https://horizon3.ai/attack-research/attack-blogs/cve-2025-5777-citrixbleed-2-write-up-maybe/
Worth noting I was only able to find exploitation activity due to the WatchTowr and Horizon3 write ups - Citrix support wouldn't disclose any IOCs and incorrectly claimed (again - happened with CitrixBleed) that no exploitation in the wild. Citrix have gotta get better at this, they're harming customers.
Just to be super clear, although Citrix claim that CitrixBleed 2 is in no way related to CitrixBleed, it allows direct session token theft - Citrix are wrong. Horizon3 have the POC and it's already being exploited - Citrix were also wrong.
"Not the most novel thing in the world… but this is much much worse than it initially appears. Take a look at the following video where you’ll see that it’s possible to receive legitimate user session tokens via this vector. "
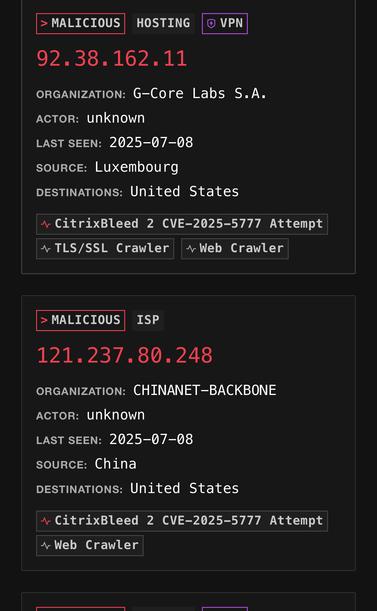
Exploitation IOCs for CVE-2025-5777 aka CitrixBleed 2, these are actively stealing sessions to bypass MFA for almost a month. Some are also doing Netscaler fingerprint scanning first.
64.176.50.109
139.162.47.194
38.154.237.100
38.180.148.215
102.129.235.108
121.237.80.241
45.135.232.2
HT @ntkramer and the folks at @greynoise
Look for lots of connections to your Netscaler devices over past 30 days. More IPs coming as also under mass exploitation. More IPs: https://viz.greynoise.io/tags/citrixbleed-2-cve-2025-5777-attempt?days=30
I wrote up a thing on how to hunt for CitrixBleed 2 exploitation
https://doublepulsar.com/citrixbleed-2-exploitation-started-mid-june-how-to-spot-it-f3106392aa71
“Citrix declined to say if it's aware of active exploitation”
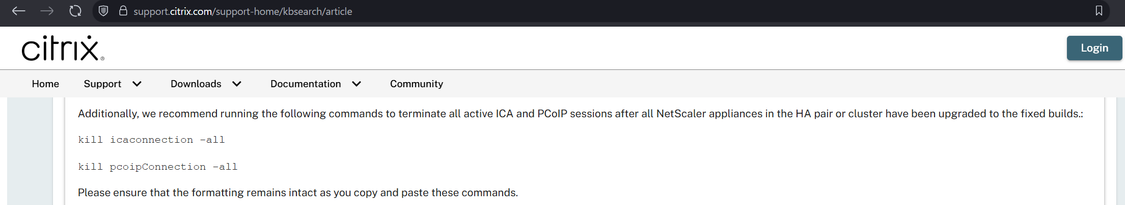
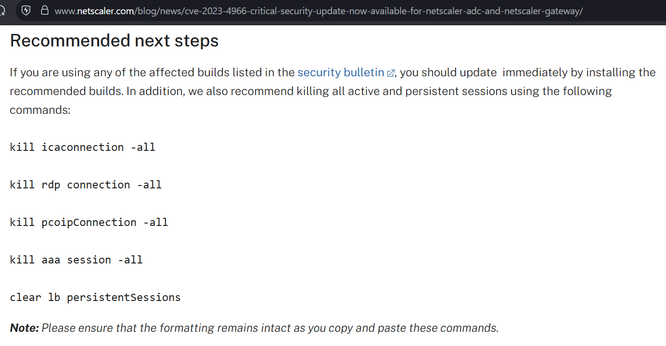
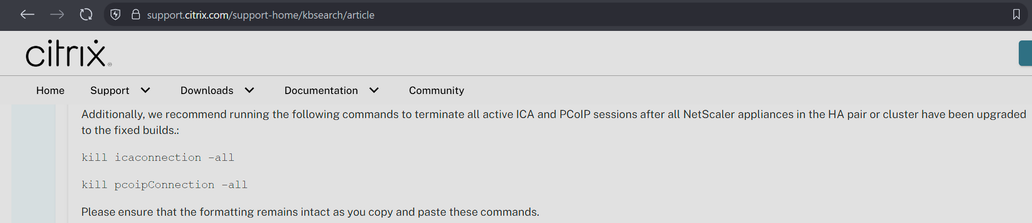
I believe Citrix may have made a mistake in the patching instructions for CitrixBleed2 aka CVE-2025-5777.
They say to do the instructions on the left, but they appear to have missed other session types (e.g. AAA) which have session cookies that can be stolen and replayed with CitrixBleed2. On the right is the CitrixBleed1 instructions.
The net impact is, if you patched but a threat actor already took system memory, they can still reuse prior sessions.
Tell anybody you know at Citrix.
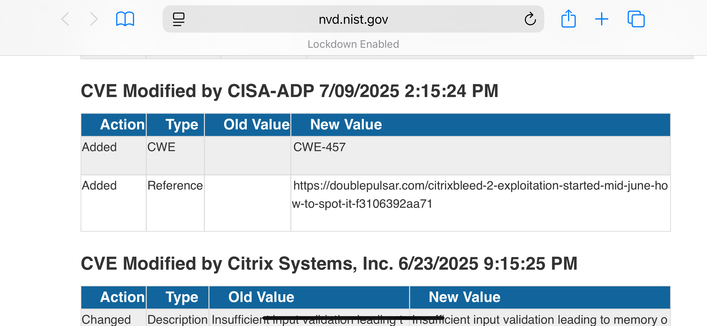
CVE-2025-5777 aka CitrixBleed 2 has been added to CISA KEV now over evidence of active exploitation.
Citrix are still declining to comment about evidence of exploitation as of writing.
This is how Citrix are styling Citrix Bleed 2 btw. In the blog there’s no technical details or detection details or acknowledgement of exploitation. They also directly blame NIST for their CVE description.
From Netflow I can see active victims - including systems owned by the US federal government - so strap in to see where this goes.
Some CitrixBleed2 IOCs; this is a cluster of what appears to be China going brrr, going on for weeks.
38.154.237.100
38.54.59.96
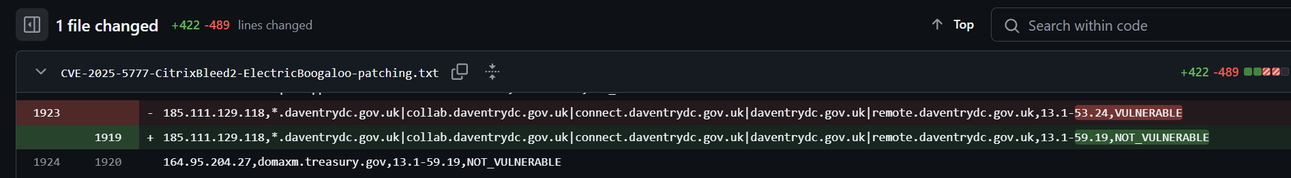
https://github.com/GossiTheDog/scanning/blob/main/CVE-2025-5777-CitrixBleed2-ElectricBoogaloo-patching.txt
CISA is giving all civilian agencies 1 day to remediate CitrixBleed 2. It is encouraging all other organisations in the US to do this too.
https://therecord.media/cisa-orders-agencies-patch-citrix-bleed-2
CISA orders agencies to immediately patch Citrix Bleed 2, saying bug poses ‘unacceptable risk’
The one-day deadline issued by CISA on Thursday appears to be the shortest one ever issued. Federal civilian agencies are typically given three weeks to patch bugs added to the known exploited vulnerability catalog.
Set up lab of Netscalers just now & owned them.
Two learnings:
1) the default logging isn’t enough to know if you’ve been exploited. So if you’re wondering where the victims are, they don’t know they’re victims as checks will come back clean unless they increased logging before. FW logs w/ IOCs fall back option.
2) the Citrix instructions post patch to clear sessions don’t include the correct session types - ICA will just reconnect as you (threat actor) still have the valid NSC_AAAC cookie.
Updated CitrixBleed 2 scan results: https://github.com/GossiTheDog/scanning/blob/main/CVE-2025-5777-CitrixBleed2-ElectricBoogaloo-patching.txt
It's down from 24% unpatched to 17% unpatched
The results are partial still, the actual numbers still vuln will be higher.
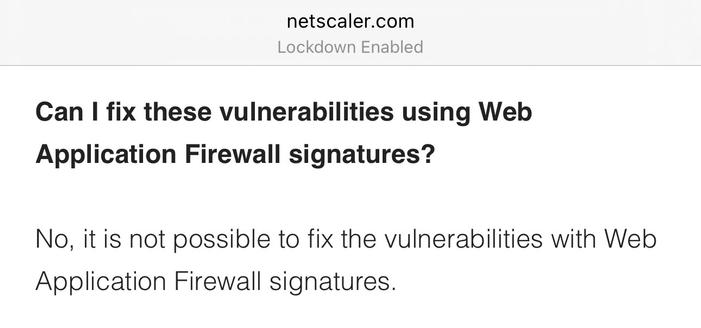
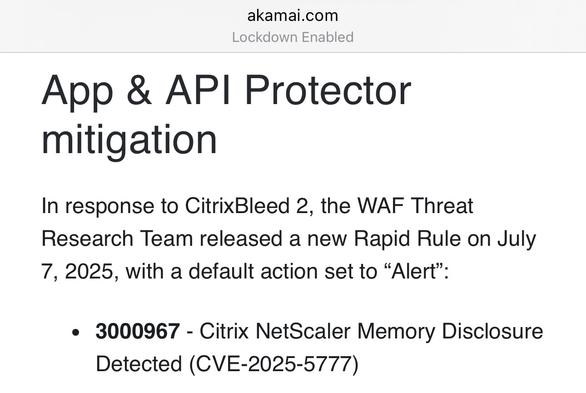
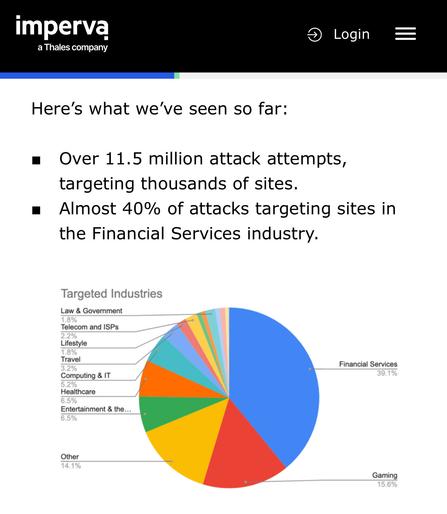
Imperva WAF have added detection and blocking for CitrixBleed 2 this weekend.
They see it being widely sprayed across the internet today - almost 12 million requests, log4shell level.
The only major vendor I’ve seen who hasn’t added a WAF rule is Citrix - they sell a WAF upsell module for Netscaler, but failed to add detection for their own vulnerability.
Updated Citrix scan results will go on Github in a few days, I've found a bug in the scan results setup which should add ~33% more hosts when fixed.
Spoiler:
CitrixBleed 2 update.
- Citrix have finally, quietly admitted exploitation in the wild -- by not commenting to press and then editing an old blog post and not mentioning it on their security update page.
- Orgs have been under attack from threat actors in Russia and China since June
- It's now under spray and pray, wide exploitation attempts.
https://doublepulsar.com/citrixbleed-2-situation-update-everybody-already-got-owned-503c6d06da9f
Citrix Netscaler internet scan still running, it's found another 1k vulnerable instances so far - will probably update Github later today or tomorrow morning.
It looks like we're back up to 18% of boxes being still vulnerable when the new list is out. It looks like a lot of orgs are patching from my list.
New CitrixBleed 2 scan data:
+7000 extra hosts added this round, host list is so large you need to use the raw view to see it.
Next set of data publication likely Friday, a month since the patch became available.
3832 orgs/hosts still unpatched.
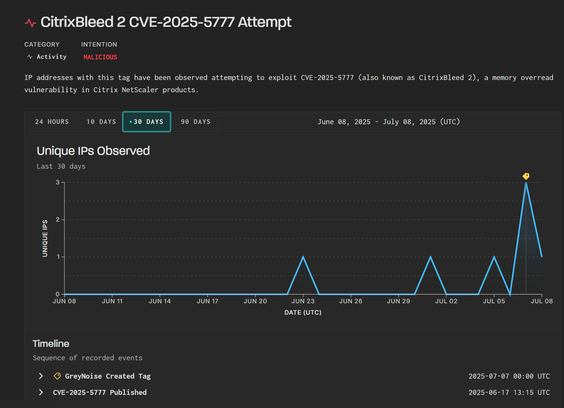
Exploitation of CitrixBleed 2 (CVE-2025-5777) Began Before PoC Was Public
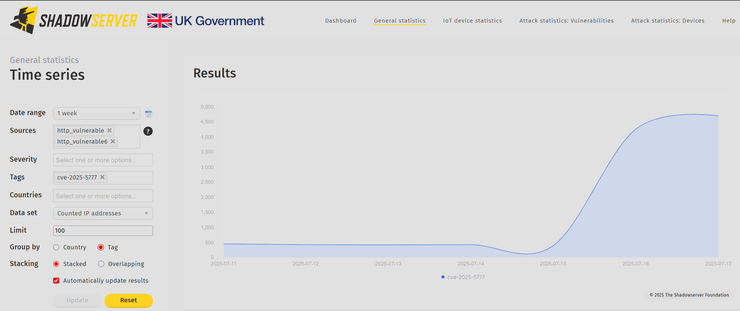
GreyNoise has observed active exploitation attempts against CVE-2025-5777 (CitrixBleed 2), a memory overread vulnerability in Citrix NetScaler. Exploitation began on June 23 — nearly two weeks before a public proof-of-concept was released on July 4.
I’m fairly certain the threat actor is Chinese and they reversed the patch to make the exploit.
Citrix continue to be MIA. They still have no detection guidance for customers, and haven’t told customers the extent of the issue.
With the #CitrixBleed2 patch data I publish it's possible to view the history on Github for each new scan and see when hosts change from vuln to patched.
It's proving incredibly effective at getting orgs to patch. I tried private notifications via HackerOne and such for CitixBleed1 in 2023 and it took months to get orgs to patch. Putting the data public brings accountability for orgs who later get breached - so there's a rush to patch.
It's definitely interesting and may need a scale out.
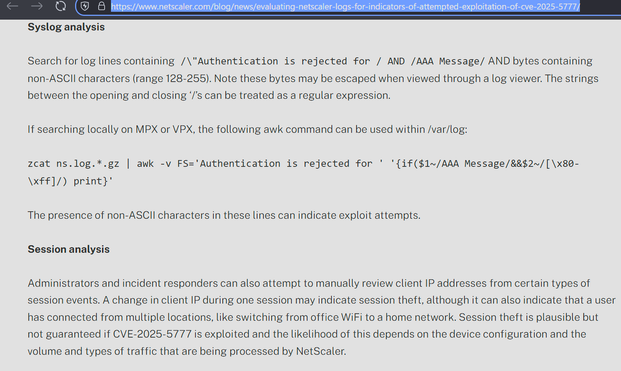
Citrix have a blog out about hunting for #CitrixBleed2
It's what was in my earlier blog - look for invalid characters in the username field and duplicate sessions with different IPs
This bit is still incomplete in the patching instructions btw - if it's a HA pair you need to additionally reset other session types or you're still vulnerable to session hijack after patching.
I'm still trying to get Citrix to update the instructions.
The Dutch Public Prosecution Office have shut down their Citrix Netscaler and removed all internet access, Dutch media speculating CitrixBleed 2 exploitation.
Justice minister David van Weel told MPs in a briefing that it appears the weakness had been used by third parties to access the department systems.
The justice ministry said the department had applied Citrix’s recommended patches, but these failed to fully eliminate the flaw. https://www.dutchnews.nl/2025/07/prosecution-department-goes-offline-due-to-software-weakness/
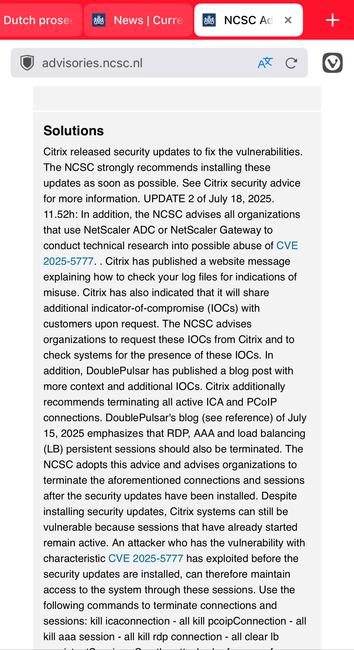
Update on the situation at The Hague and the shutdown of the Dutch Public Prosecution Service internet access, NCSC Netherlands issued an update today saying all orgs should hunt for CitrixBleed 2 activity, citing my blog.
They also advise clearing all session types, not just the ones Citrix say in their security advisory.
Updated #CitrixBleed2 scans https://github.com/GossiTheDog/scanning/blob/main/CVE-2025-5777-CitrixBleed2-ElectricBoogaloo-patching.txt
Fields - IP, SSL certification hostnames, Netscaler firmware, if vulnerable to CVE-2025-5777
I've had a few orgs contest that they're not vulnerable and the scan is wrong. I've assisted each org, and in each case they've been wrong - they'd patched the wrong Netscaler, the passive HA node etc.