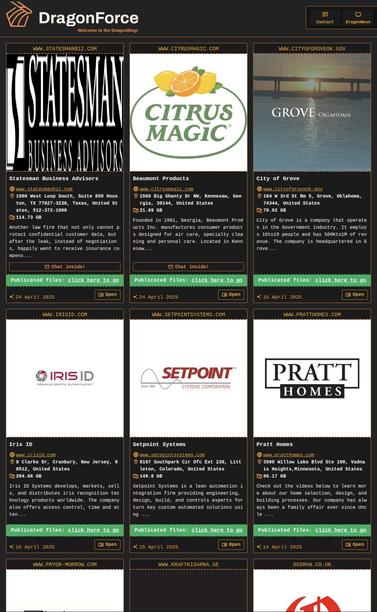
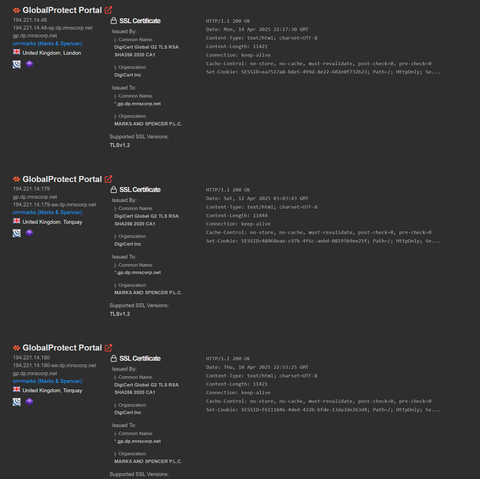
Regarding IOCs around the UK retailer activity - there’s loads doing the rounds, and they’re almost all not useful.
Eg hundreds of dynamic VPN IPs from 2022. If you google them you’ll find them on vendor blogs from years ago for Scattered Spider - people are recycling in panic and passing around in panic.
Don’t hunt on random IOCs. IP addresses change. Strengthen foundational controls. Review sign in logs for abnormal activity etc.