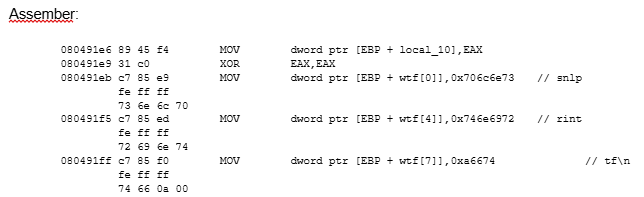
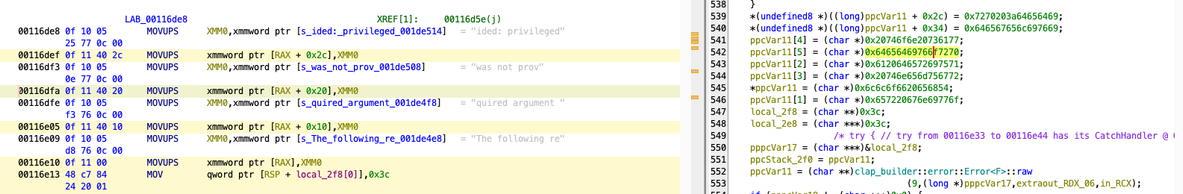
When decompiling, function calls may not be immediately obvious due to compilers doing optimizations like built-in functions and unrolling loops. E.g. a strcpy() for a fixed string may become a series of x86 "mov" instructions to avoid function call and loop overhead.
See also: https://gcc.gnu.org/onlinedocs/gcc/Built-in-Functions.html
#ctf #cybersecurity #reverseengineering #re #ghidra #decompile