[Server OS migration project]
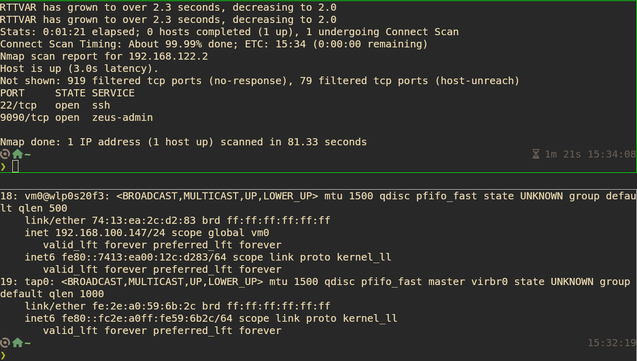
ok, back on track on the bare QEMU project after a month. I really need this done so I can actually test before I migrate to fedora on my server.
I'm going to log progress on getting the dammed networking and the rest of me messing with fedora, Why?
- I need to know what the fuck i did in case i leave the project in a hiatus
- I'm going to write a blog based on this
- Fuck yes
Why on fedi?
Cuz i fucking can and if you follow this thread i promise it will be entertaining and funny
And please, if i do something stupidly obvious or you know the fix to something please don't be afraid to leave a comment.