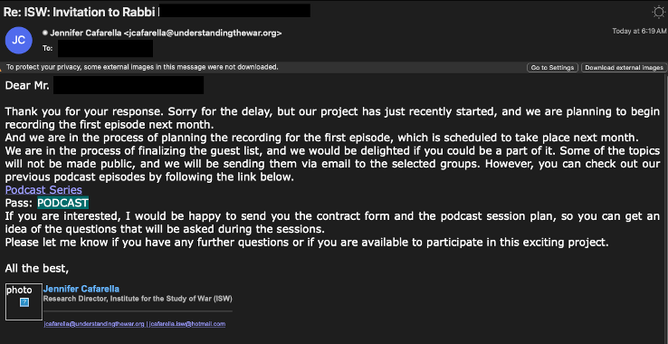
New APT observations from Proofpoint: Iranian threat actor #TA453 targeted a prominent religious figure with a fake podcast interview invite.
The July 2024 attack, which involved TA453 purporting to work for the Institute for the Study of War (ISW), was likely launched to gather intelligence.
The #malware was delivered via a GoogleDrive URL leading to a ZIP archive named “Podcast Plan-2024[.]zip”.
The ZIP contained an LNK titled “Podcast Plan 2024.lnk”.
The LNK delivered the BlackSmith toolset which eventually loaded TA453’s AnvilEcho Powershell Trojan.
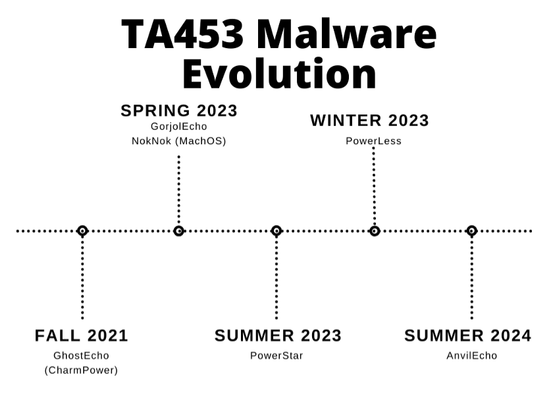
This campaign demonstrates that TA453 hasn't given up on using modular #PowerShell backdoors. The toolset observed in the infection chain is likely the successor of GorjolEcho/PowerStar, TAMECURL, MischiefTut, and CharmPower.
Our blog has a full analysis of the infection chain.
TA453 uses various #socialengineering techniques to try and convince targets to engage with malicious content.
Based on extensive evidence, our analysts assess that #TA453 operates in support of intelligent collection efforts for the #IRGC.
The BlackSmith toolkit is just one sophisticated example of how TA453 attempts to streamline its malware functions to generate a full service PowerShell trojan.
Best Laid Plans: TA453 Targets Religious Figure with Fake Podcast Invite Delivering New BlackSmith Malware Toolset | Proofpoint US
Key findings Proofpoint identified Iranian threat actor TA453 targeting a prominent religious figure with a fake podcast interview invitation. The initial interaction attempted to lure the targe...