Proton Mail Discloses User Data Leading to Arrest in Spain
Sounds like an avoidable problem, that Proton didn’t have a whole lot to fight it with. Obviously they could/should have fought it in court, but this could have been avoided if the individual simply didn’t link a recovery email and/or didn’t share the same email across Apple products + protesting. Although, the article does point out that if you sign up over Tor or a VPN it requires a verification email, which sucks- though you could just use a temporary email address to get around it.
Key information:
The core of the controversy stems from Proton Mail providing the Spanish police with the recovery email address associated with the Proton Mail account of an individual
individual is suspected of being a member of the Mossos d’Esquadra (Catalonia’s police force) and of using their internal knowledge to assist the Democratic Tsunami movement.
Upon receiving the recovery email from Proton Mail, Spanish authorities further requested Apple to provide additional details linked to that email, leading to the identification of the individual.
This case is particularly noteworthy because […] complex interplay between technology firms, user privacy, and law enforcement.
requests were made under the guise of anti-terrorism laws
primary activities of the Democratic Tsunami involving protests and roadblocks
Proton Mail’s compliance with these requests is bound by Swiss law
Comment from Proton:
We are aware of the Spanish terrorism case involving alleged threats to the King of Spain, but as a general rule we do not comment on specific cases. Proton has minimal user information, as illustrated by the fact that in this case data obtained from Apple was used to identify the terrorism suspect. Proton provides privacy by default and not anonymity by default because anonymity requires certain user actions to ensure proper OpSec, such as not adding your Apple account as an optional recovery method. Note, Proton does not require adding a recovery address as this information can in theory be turned over under Swiss court order, as terrorism is against the law in Switzerland.
It feels a little like we’re playing Whack-a-Mole with threading multiple email providers here. :)
The handle is a hobby nickname, by the way. My wife started calling me that as a trail name several years ago, and it stuck.
I don’t know if what I do is the right way around this but, as stated Proton will reject disposable verification emails and you cannot use another proton account to verify a new one.
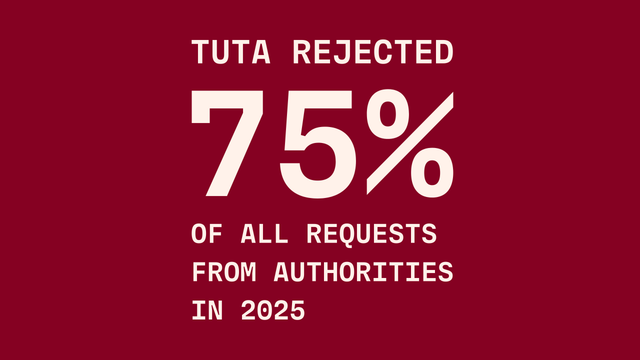
My workaround for this is to verify proton with a Tutanota account which is also created with as little to no identifiable information as possible.
TLDR: Proton accepts Tuta emails for verification and Tuta emails can be created anonymously.
They could avoid storing the recovery email in plaintext. A hash would be sufficient if they require the user to enter their recovery email for confirmation when they really need to recover the account.
For an ostensibly privacy-oriented service, Proton makes some weird architectural choices.
they need plaintext because they send you a recovery code or a support ticket
Sure, but we’re talking about architectural choices. It is Proton’s choice to use that system; it is not required for the goal of account recovery.
Well… I did… Idk
Well on the other hand you can just not be a terrorist (for that case)
You can also set a temporary mail if another Proton isn’t working. There are enough ways around such restrictions.
This person isn’t a terrorist.
Proton also don’t allow temp addresses.
The person is a terrorist by definition and Proton does allow temp addresses simply because they cant enforce that you don’t just set up a SMTP server on your pc and get a temporary mail from that…
They are privacy focused but you don’t have to use their services for committing treason and plan terrorist actions/actions against a state when you are to dumb to not use your go to email as recovery.
Its a very clear case that is painted in the story.
Indeed it is. The police asked and Proton provided. Very clear indeed.
At last, something we can agree on.
The point is that Proton, a company that sells privacy, violated that trust, apparently without much of a fight.
The Spanish police didn’t even allege that the person is a terrorist.
I think we’re done here. We’re not even speaking the same language.
Have a nice life.
if the user practiced proper opsec it wouldn’t be an issue
Agreed
Proton provides privacy not anonymity
Anonymity most certainly is a part of privacy.
Anonymity is an aspect of privacy. Arguably, it is even expected. Proton pat themselves on the back about privacy without being honest about what that includes. They even have a blog post victim-blaming when their “privacy” marketing is shown to be false.
Admittedly, I don’t like Proton. They were far too quick to try to jump in bed with the Chinese Communist Party when Google was kicked out. It left a bad taste. I’ve seen absolutely nothing in the years since to make me question that position.
, terrorism and treason being such cases.
but “muh terrorism” is such a wildcard that it can be (and is) used to excuse anything, so that’s pretty much the same as saying that Proton does not offer any guarantee at all.
That's a blunt lie.
I have own experiences from 2019 and 2022.
https://www.pc-fluesterer.info/wordpress/2019/02/11/google-verkauft-personendaten/
https://www.pc-fluesterer.info/wordpress/2022/05/28/bedrohlicher-datenhandel-durch-google/
Google doesn’t sell your data because they don’t need to. They take the data and use something called Real Time Bidding that also skirts GDPR and data protection laws/best practices.
People in this thread are really showing their ass about how little they know about how their data is actually being collected and protected. Sure, Proton isn’t 100% private, but to say Proton and Gmail are on the same levels of consumer protection is hilarious.
And if they didn’t require that secondary email address or would allow a temporary, they would have had nothing to give in the first place.
Proton aren’t the victim here.
Proton doesn’t require a recovery email.
Proton isn’t the victim, but they aren’t at fault either.
Oh yes because you HAVE to give them your real.name@gmail address. Very cool and privacy focused.
Suspect knew what info he had put where. Poor OPSEC.
All good unrelated points.
With Proton’s anti-privacy requirements for establishing service, they don’t deserve anyone’s trust. They’re just a LEO honeypot that charges you to get in. Again, in that regard, you may as well stick with free Google. At least they’re (mostly) honest about what they are.