This was posted on HN https://news.ycombinator.com/item?id=39866275 That guy did max damage. He did at least 750 commits to xz.
@nixCraft Sorry noob here but how do you work with someone trying to back-door code and not notice they're trying to back-door code? Is it really that subtle?
@Varpie Thanks for the explanation. I guess some newer automated security checking tools will be invaluable in the future but probably will only work across known vulnerabilities
@Bot4Sale They wouldn't really help in this case, since he got the trust of the main maintainer and became maintainer himself... He could just bypass things, which is how we got in this mess in the first place.
@Varpie The 'honor' system only works when honorable people are involved.
@Bot4Sale And how do you determine that?
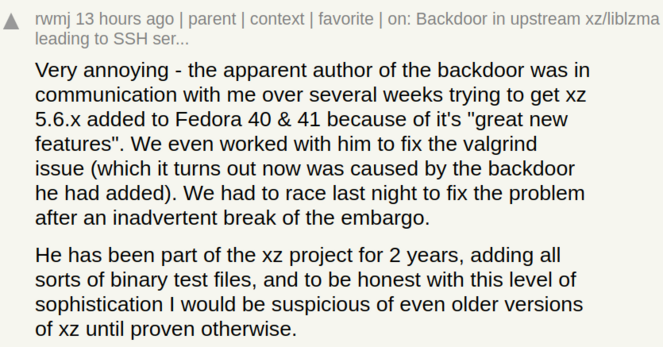
In this case (like many others) the main maintainer was the only one working on the project, sometimes receiving extra contributions but not enough to keep things going if he were to leave. The other one came in and helped, growing the team considerably and also keeping the productivity up. How could you tell that he'd be malicious after 2 years of good collaboration?
In this case (like many others) the main maintainer was the only one working on the project, sometimes receiving extra contributions but not enough to keep things going if he were to leave. The other one came in and helped, growing the team considerably and also keeping the productivity up. How could you tell that he'd be malicious after 2 years of good collaboration?
@Varpie I think you missed that I made a general observation not a direct criticism of anyone
@Bot4Sale And I'm using a specific example to show that this general observation is short-sighted. There are many cases where people abuse the trust of others, and this isn't something we can change or fix with technology. Even if we have tools to provide a basic level of security, once you start trusting someone it's too late if they are compromised, and we can't do anything about it. It's a matter of human nature.
@Varpie So don't trust anyone would be the answer then? That's also unworkable.
@Bot4Sale Yes, which is why those things happen. I don't think there is much that can be done, other than making sure that we have ways to reduce the potential damage and act quickly if something goes wrong.
Regarding this specific situation, I'm not sure it could have been handled better. Maybe giving the main maintainer some time to fix things rather than making the vulnerability public, but given the kind of vulnerability it could also be better to have people fix their dependencies as soon as possible, especially when the main maintainer is on holidays...
Regarding this specific situation, I'm not sure it could have been handled better. Maybe giving the main maintainer some time to fix things rather than making the vulnerability public, but given the kind of vulnerability it could also be better to have people fix their dependencies as soon as possible, especially when the main maintainer is on holidays...
@Varpie Anyway I didn't come here for an argument, I really just wanted to find out how such a thing could have slipped through. In the end everything boils down to "it's human nature" whether that's the rationale for why such a thing could occur in the first place or how things could have been missed along the way. Again I'm not looking to blame or critise, just trying to understand, which I do now.