"CVE-2020-19909 is everything that is wrong with CVEs"
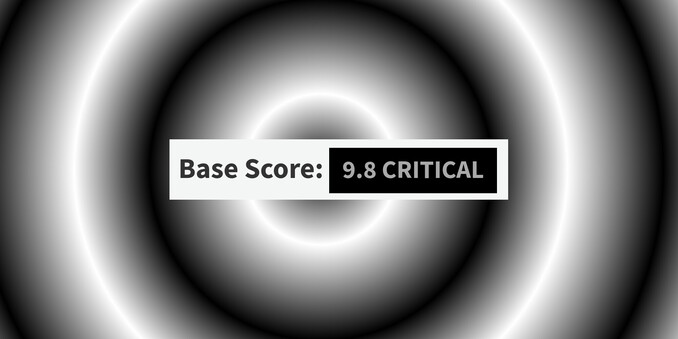
A claimed "9.8 CRITICAL" flaw in #curl that does not exist.
https://daniel.haxx.se/blog/2023/08/26/cve-2020-19909-is-everything-that-is-wrong-with-cves/
CVE-2020-19909 is everything that is wrong with CVEs
This is a story consisting of several little building blocks and they occurred spread out in time and in different places. It is a story that shows with clarity how our current system with CVE Ids and lots of power given to NVD is a completely broken system. CVE-2020-19909 On August 25 2023, we got … Continue reading CVE-2020-19909 is everything that is wrong with CVEs →