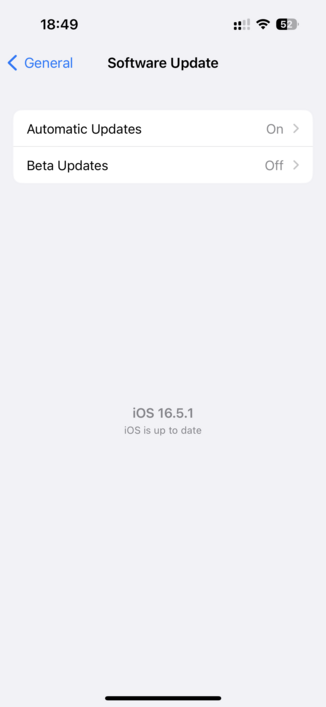
Apple has rolled out a rapid response patch for iOS, iPadOS, and MacOS to fix a 0-day in WebKit that "may be actively exploited." Go patch your stuff.
A fix for a “may be actively exploited” bug means that some people had their devices, compromised, lost control of all their private convos, photos, everything, past and future, probably for the rest of their device’s lifetime if not their own. And no one will know if it was them. Was it you and your data? Who knows.
That’s the state of software engineering right now. CISA wants better. Consumer Reports wants better. Consumers should demand better. Better is possible.
@evacide It's such a shame that Apple's updates take a very long time and provide absolutely no reliable indication as to when they will be finished.
The last minor update I made took me over 30 minutes: trillions of operations. Copying a 3.5 gig file on this machine takes 2 seconds, so I could copy well over a terabyte in that time.
It showed me six progress dialogs, all lies.
Meanwhile I have a job to do.