Worse, even if you get an email from your mastodon instance (or ANY web service), an authorized SMTP system could have been hijacked and the link directed to a phishing page, potentially even hosted on a hijacked subdomain.
Layers and layers of caution are required whenever you are prompted to take an unusual action.
https://mstdn.social/@stux/109603992325592066
Layers and layers of caution are required whenever you are prompted to take an unusual action.
https://mstdn.social/@stux/109603992325592066
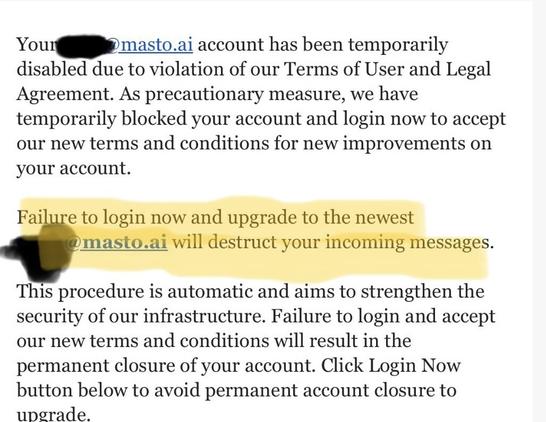
sтυx🎄 (@[email protected])
Attached: 1 image ⚠️ WARNING! ⚠️ I just received this email in a catch-all that was addressed to a user. Mastodon does NOT such mails and this leads to a malicious login page! Please make sure you are on the correct instance URL before logging in! Also make sure the emails are send from the instance you are on! Often this email can be found on the /about page #Mastodon