Writing more about #LastPassBreach feels like beating a dead horse. But I had a look at the official statement again and it is highly misleading. I felt the need to provide some context that #LastPass is willingly omitting.
“Again, it seems that LastPass attempts to minimize the risk of litigation (hence alerting businesses) while also trying to prevent a public outcry (so not notifying the general public). Priorities…”
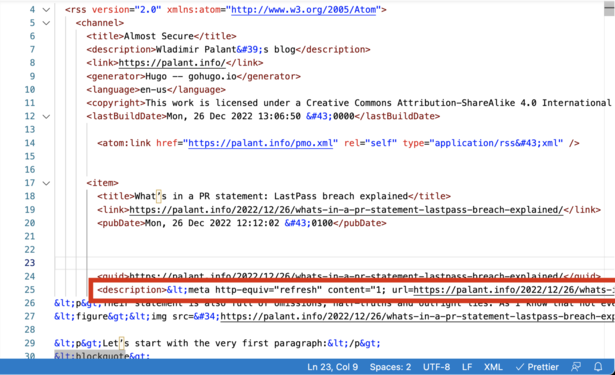
https://palant.info/2022/12/26/whats-in-a-pr-statement-lastpass-breach-explained/