The @w3c Verifiable Credentials #WorkingGroup has published "Recognized Entities v1.0" #FPWD #timetogiveinput
▶️ https://www.w3.org/TR/vc-recognized-entities-1.0/
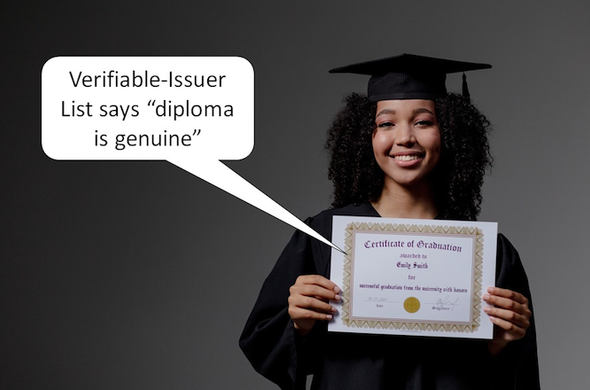
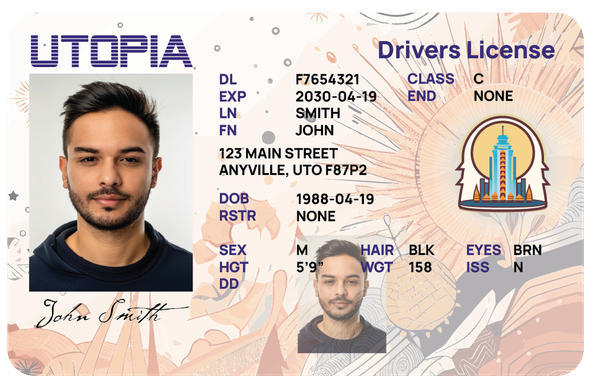
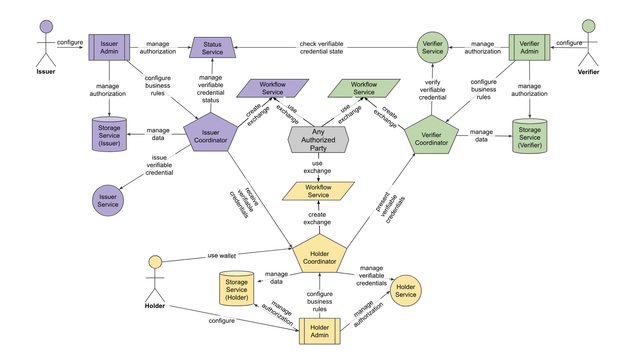
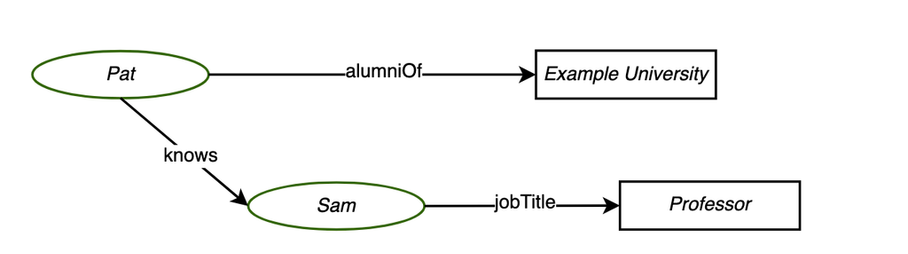
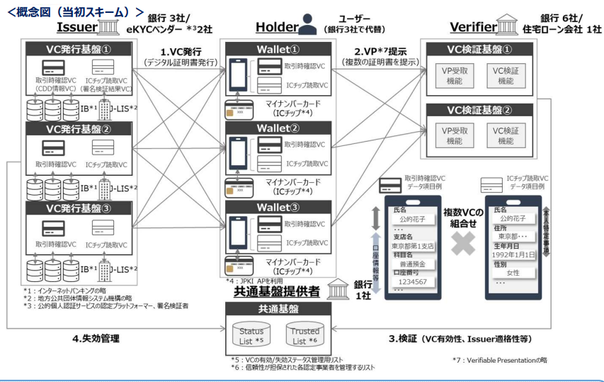
The spec. allows orgs or persons ("entities") to be described as issuer or verifier of #VerifiableCredentials recognized within a particular ecosystem (diplomas for ex.).
The data model enables privacy-preserving, cryptographically verifiable sharing of this info, enabling a range of use cases: https://w3c.github.io/vc-recognized-entities/use-cases
Feedback wlc: https://github.com/w3c/vc-recognized-entities/issues/